Verizon’s Call Filter Blunder: A Comedy of Errors in Call Log Security
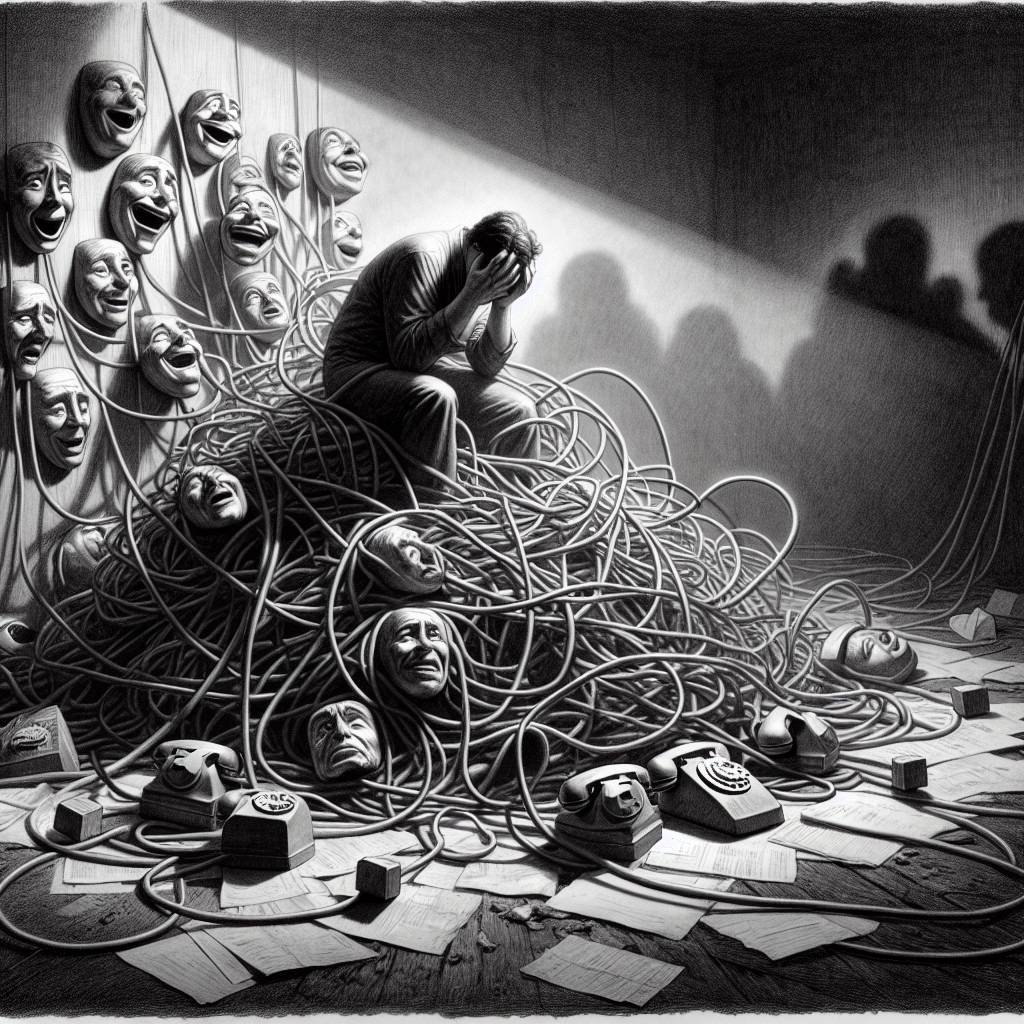
Verizon’s Call Filter app had a vulnerability that let users peek at others’ call logs like a nosy neighbor with x-ray glasses. Discovered by Evan Connelly, this flaw could turn any Verizon customer into Sherlock Holmes with a smartphone. Verizon fixed it, but the exposure window remains a mystery.
Hot Take:
In the latest episode of “Oops, We Did It Again,” Verizon found itself in a pickle with a Call Filter feature that was more like a Call Free-for-All! Who knew that while trying to block spam, you could inadvertently turn your customers’ call logs into the hottest gossip column in town? Next time, Verizon, maybe filter out the security risks too!
Key Points:
- Verizon’s Call Filter app had a vulnerability allowing access to others’ incoming call logs.
- The bug was discovered by researcher Evan Connelly and was fixed within a month.
- The flaw was due to an unsecured API endpoint, impacting potentially millions of users.
- The vulnerability posed risks for high-value targets like politicians and journalists.
- The API was hosted by Cequint, a company with limited public information and an offline website.
Already a member? Log in here
