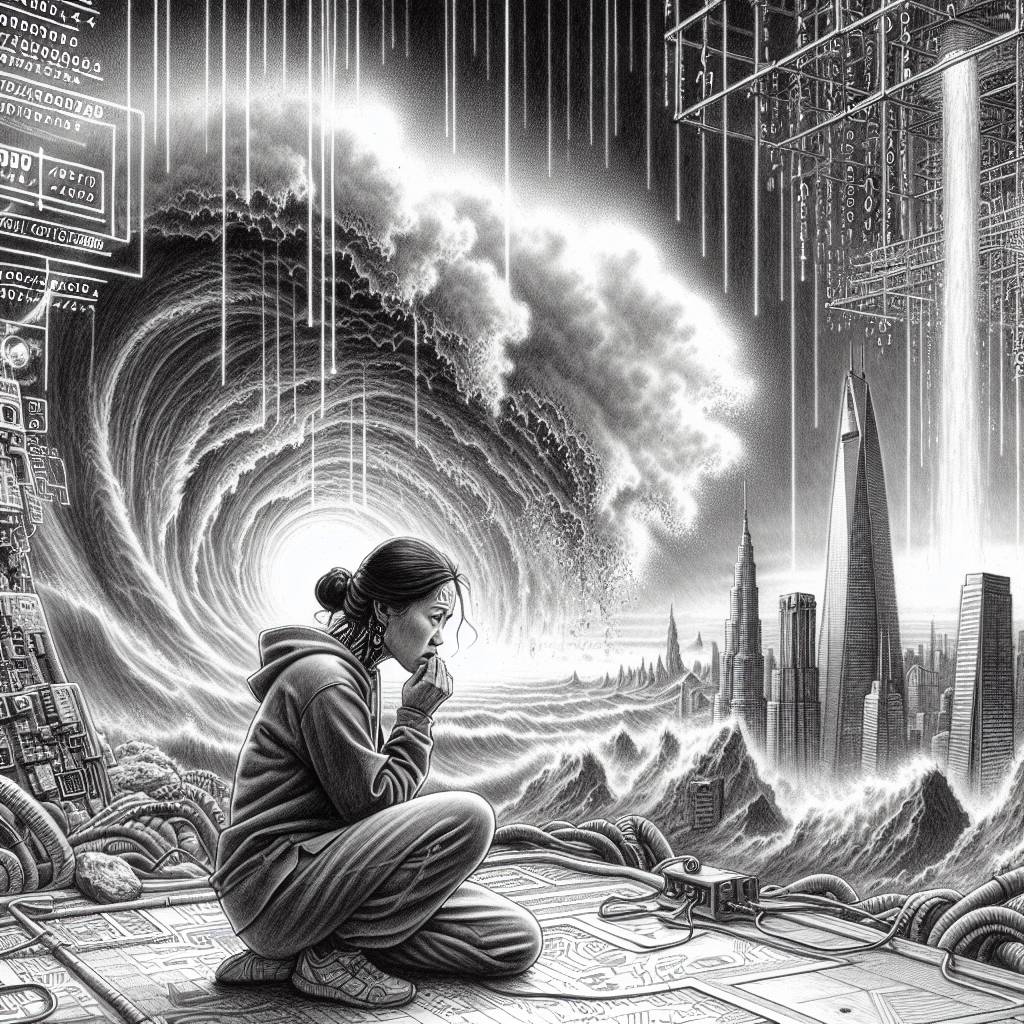
Veeam’s Critical Flaw: Update Now or Risk Remote Code Chaos!
Veeam has patched a critical flaw in its Service Provider Console (VSPC) that could enable remote code execution. With a CVSS score of 9.9, this vulnerability, CVE-2024-42448, was discovered during internal testing. Users should upgrade to the latest version immediately to avoid ransomware attacks exploiting these Veeam vulnerabilities.
Hot Take:
Looks like Veeam just dropped a security bombshell with their latest updates! If you’re using their Service Provider Console, you might want to update faster than you can say “remote code execution” – or risk your systems becoming a hacker’s new playground!
Key Points:
- Veeam has released critical security updates for its Service Provider Console.
- The vulnerability, CVE-2024-42448, has a CVSS score of 9.9 out of 10.
- It allows for Remote Code Execution (RCE) on VSPC server machines.
- A second flaw, CVE-2024-42449, can leak an NTLM hash and delete files.
- Users must upgrade to version 8.1.0.21999 for protection.
Already a member? Log in here
