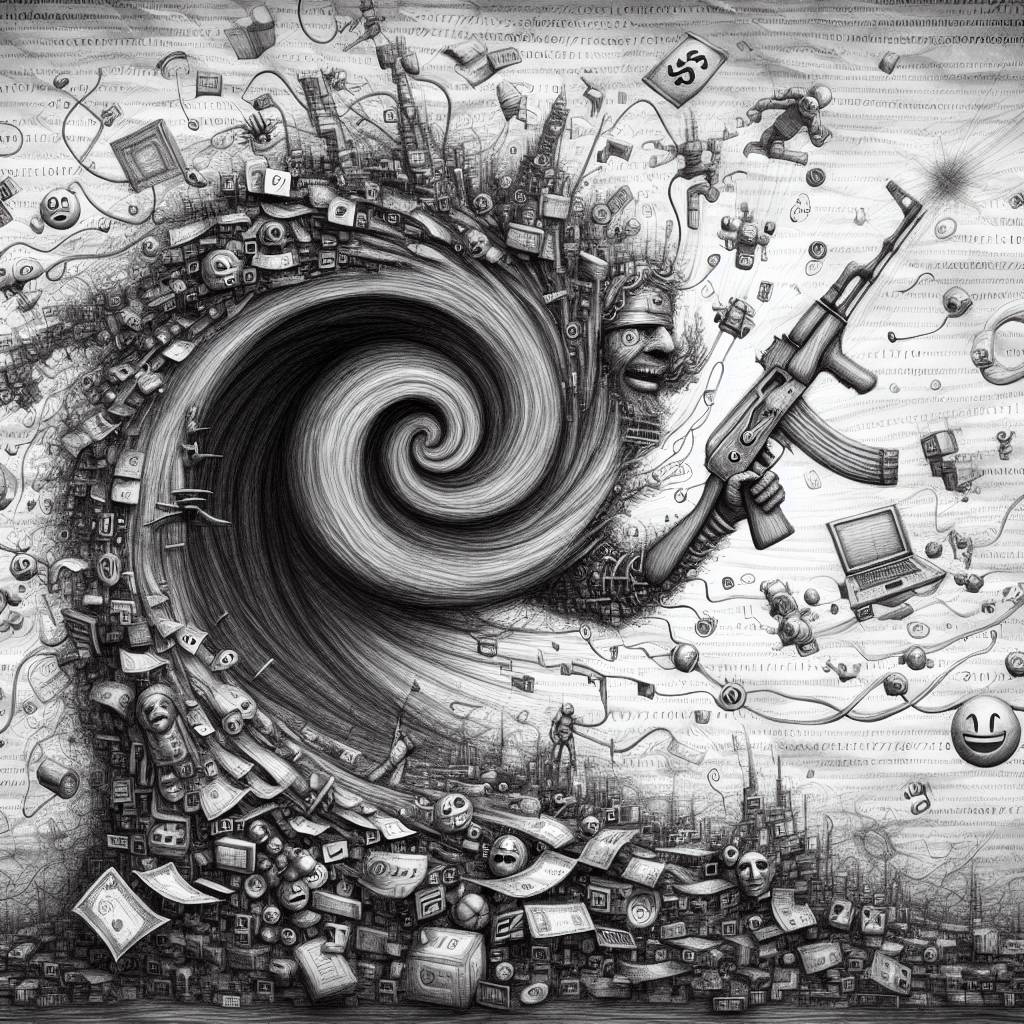
Storm-2603 Unleashes AK47 C2: A Comedic Take on Cyber Espionage Meets Ransomware Chaos!
Storm-2603, a suspected China-based cyber threat actor, is shaking up the scene with its custom AK47 C2 framework. Using SharePoint flaws, they’ve been deploying Warlock ransomware like it’s going out of style. With a penchant for DLL hijacking and open-source tools, this group is blurring lines between espionage and crime.
Hot Take:
***Ah, Storm-2603, the digital Swiss Army knife of cyber mischief! With their AK47 C2 framework, they’re not just exploiting Microsoft SharePoint flaws; they’re hosting a hacker’s variety show. From deploying Warlock ransomware to sideloading DLLs like it’s a tech demo, these folks are proving that when it comes to cybercrime, versatility is key. Who knew being a threat actor could have such a comprehensive resume?***
Key Points:
– Storm-2603 is exploiting Microsoft SharePoint security flaws with a custom C2 framework called AK47 C2.
– The operation uses two types of clients: AK47HTTP and AK47DNS.
– The threat group has been linked to deploying ransomware families like Warlock and LockBit Black.
– They employ techniques like DLL hijacking and BYOVD to disable defenses and deploy malware.
– Their exact motivations remain unclear, making them a wild card in the cyber threat landscape.
