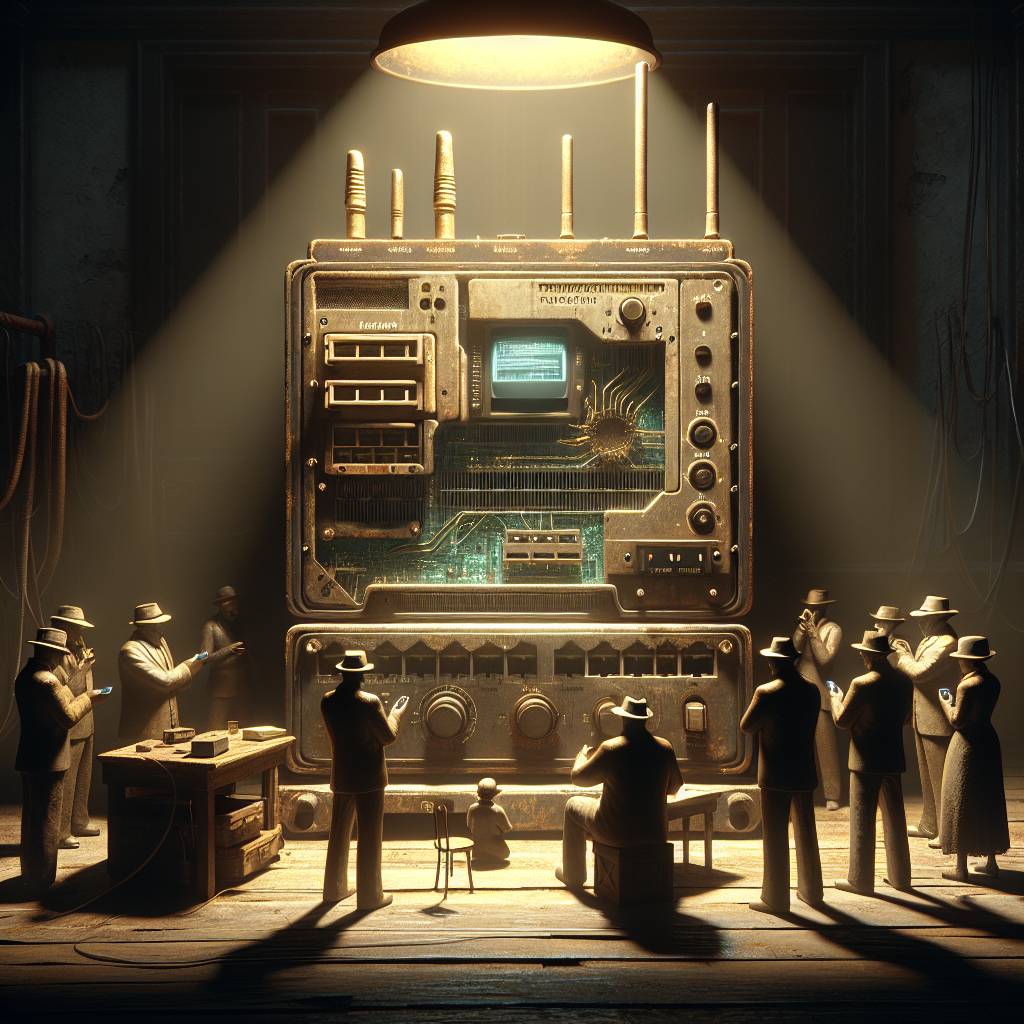
Smishing Shenanigans: How Hackers Exploit Routers for European SMS Scams!
Unknown threat actors are exploiting Milesight industrial routers to send smishing messages in Europe, using the router’s API to distribute phishing URLs. The attack primarily targets Sweden, Italy, and Belgium with typosquatted URLs mimicking official platforms. These routers, weak on security, have become the smishing campaign’s unwitting wingmen.
Hot Take:
It looks like the threat actors have taken a page out of the classic playbook: “If it ain’t broke, don’t fix it.” Why spend time forging new tools when you can just hijack someone else’s? Milesight routers, congratulations, you’ve officially become the Uber of smishing campaigns, ferrying phishing URLs to unsuspecting Europeans faster than you can say “typosquatted URLs!”
Key Points:
– Threat actors are exploiting Milesight routers to send smishing messages across Europe.
– Vulnerable routers expose SMS features without authentication, making them easy targets.
– Attackers use typosquatted URLs to impersonate government and financial institutions.
– The used flaw (CVE-2023-43261) was disclosed two years ago, but only recently weaponized.
– Phishing URLs include JavaScript to evade detection and log visitor data to a Telegram bot.
