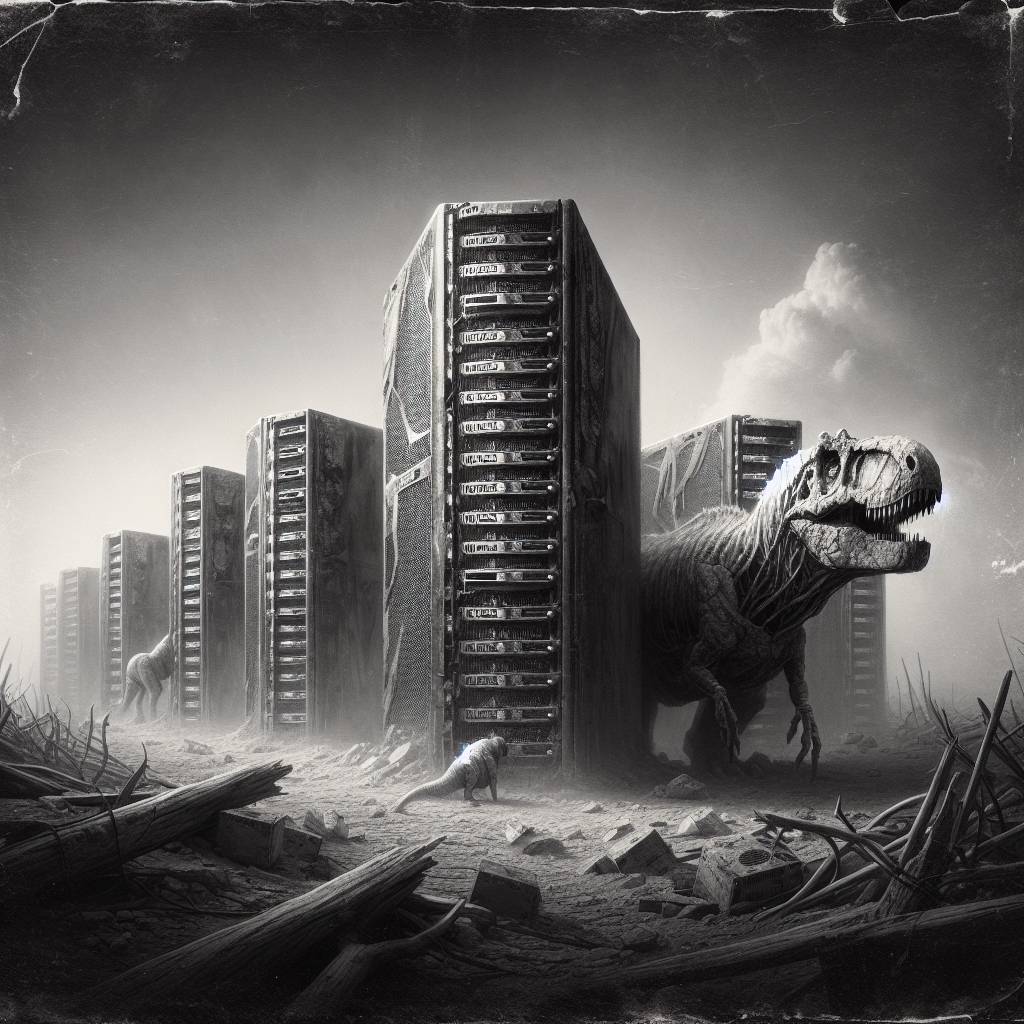
Say Goodbye to Your IT Dinosaurs: NCSC’s Guide to Safe and Secure Decommissioning
When IT assets reach their twilight years, the National Cyber Security Centre’s guide is your go-to companion. Safely decommission end-of-life IT assets to avoid cyber mishaps, prevent rogue routers from joining botnets, and ensure your backup plans aren’t just a dusty binder in the corner. Remember, even expired tech can cause fresh headaches!
Hot Take:
Who knew that saying goodbye to your old IT gear could be more complicated than a celebrity breakup? The NCSC just published a guide to retiring end-of-life IT assets, and it’s as thrilling as a plot twist in a daytime soap opera. Remember folks, don’t let your old routers haunt you like a ghost of WiFi past!
Key Points:
- The NCSC has released a guide to safely retire end-of-life IT assets.
- Proper decommissioning is critical to prevent unauthorized access or exploitation.
- Assets need to be accurately identified and associated records validated.
- Secure storage, effective communication, and coordination are essential steps.
- Post-decommissioning verification and monitoring are crucial to avoid unforeseen impacts.
Already a member? Log in here
