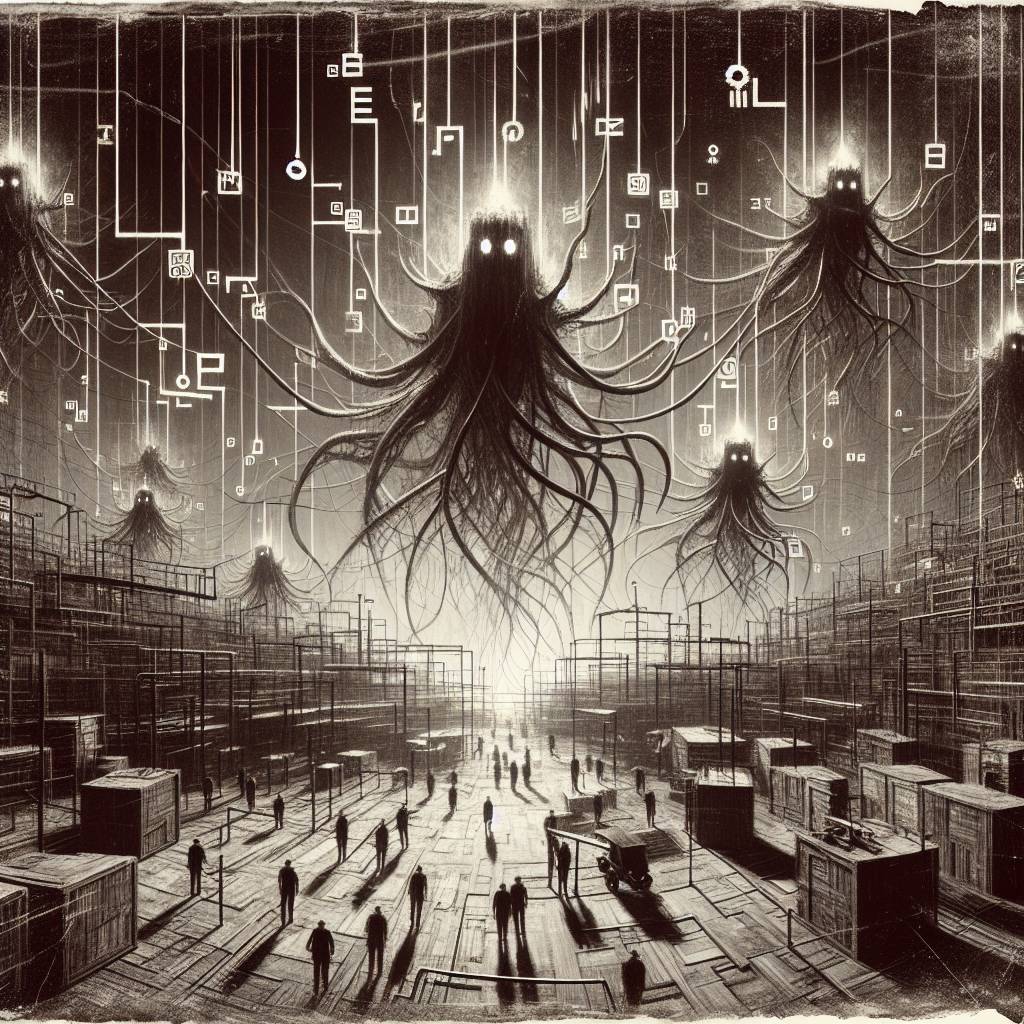
Russian Hackers Turn Ukrainian Networks into a Digital Hide-and-Seek Playground
Russian hackers, likely linked to Sandworm, used living-off-the-land tactics and dual-use tools to infiltrate Ukrainian targets. They slipped past defenses using legitimate applications, proving once again that sometimes the best way to hack a system is to act like you belong there, with a clipboard and a suspiciously confident stride.
Hot Take:
**_When it comes to espionage, Sandworm is like the James Bond of the cyber world—minus the tuxedos and martinis, but definitely with the same sneaky flair. They’ve swapped out gadgets for legitimate tools, making it hard for Ukrainian targets to tell if they’re being hacked or just having a bad day at the IT office. Who knew cyber warfare could be so… incognito?_**
Key Points:
– Russian hackers, likely linked to Sandworm, targeted Ukrainian firms using LOTL (Living-off-the-land) tactics and dual-use tools.
– Attackers infiltrated a Ukrainian business services firm for two months and a local government for a week.
– They exploited unpatched vulnerabilities to plant webshells like Localolive, previously linked to Sandworm.
– The attackers used minimal malware to evade detection while maintaining long-term network access.
– They demonstrated deep Windows knowledge to steal credentials and employed legitimate tools like OpenSSH and PowerShell.
