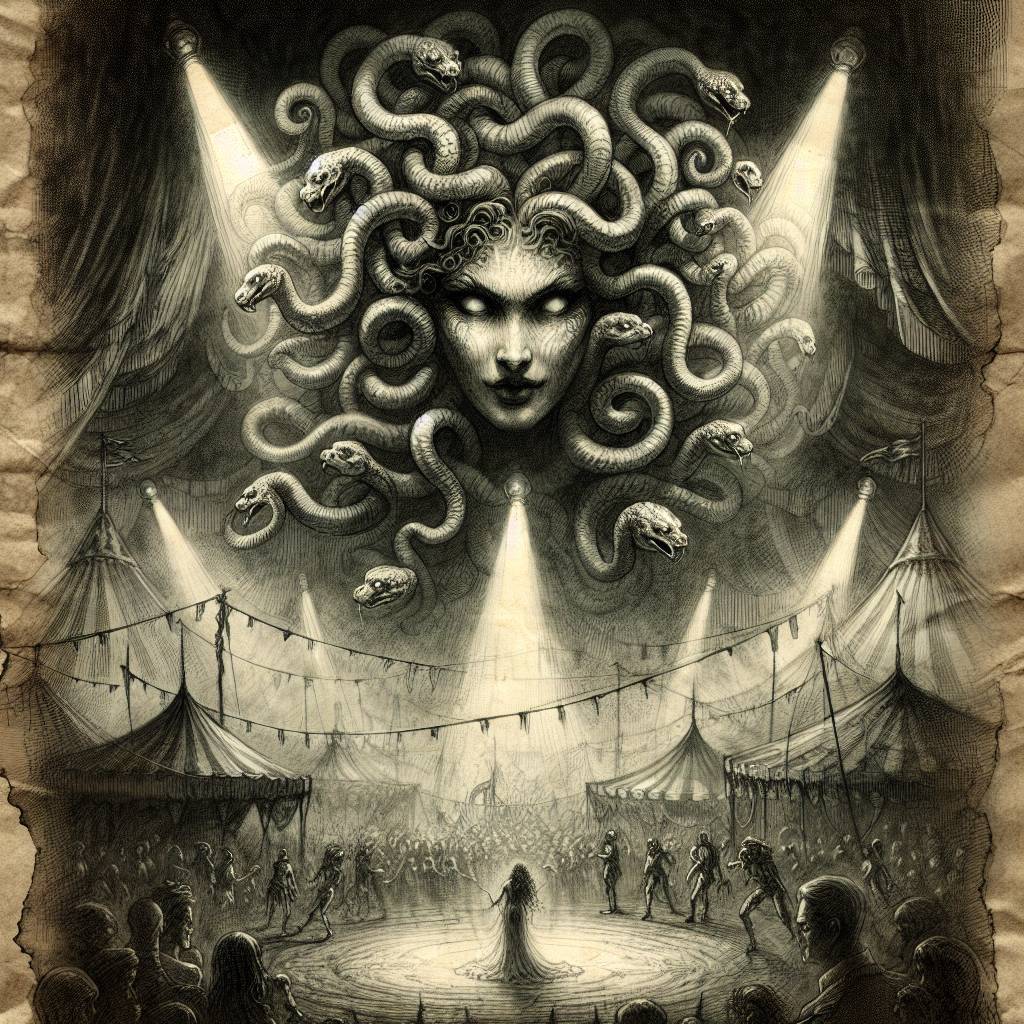
Ransomware Rodeo: Medusa’s Malicious Driver Circus Unmasked!
The Medusa ransomware gang is now using ABYSSWORKER, a malicious driver, to stage BYOVD attacks that silence security tools. Like a mischievous magician, it distracts antivirus software with revoked certificate-signed drivers and performs a vanishing act on security defenses, enabling attackers to waltz in and exfiltrate sensitive data.
Hot Take:
Who knew that ransomware had an underground DJ scene? Medusa’s new BYOVD (Bring Your Own Vulnerable Driver) attack is spinning its malicious tracks with ABYSSWORKER, a driver that makes anti-malware software hit the dance floor in defeat. It’s like cybersecurity’s version of musical chairs, but with more chaos and less furniture.
Key Points:
- Medusa ransomware uses a bring your own vulnerable driver (BYOVD) tactic.
- ABYSSWORKER, a malicious driver, mimics legitimate software to evade detection.
- Stolen, revoked certificates from Chinese companies add a false sense of trust.
- Threat actors exploit kernel driver vulnerabilities for elevated system privileges.
- RansomHub ransomware affiliates use multi-function backdoor, Betruger, for stealth attacks.
Already a member? Log in here
