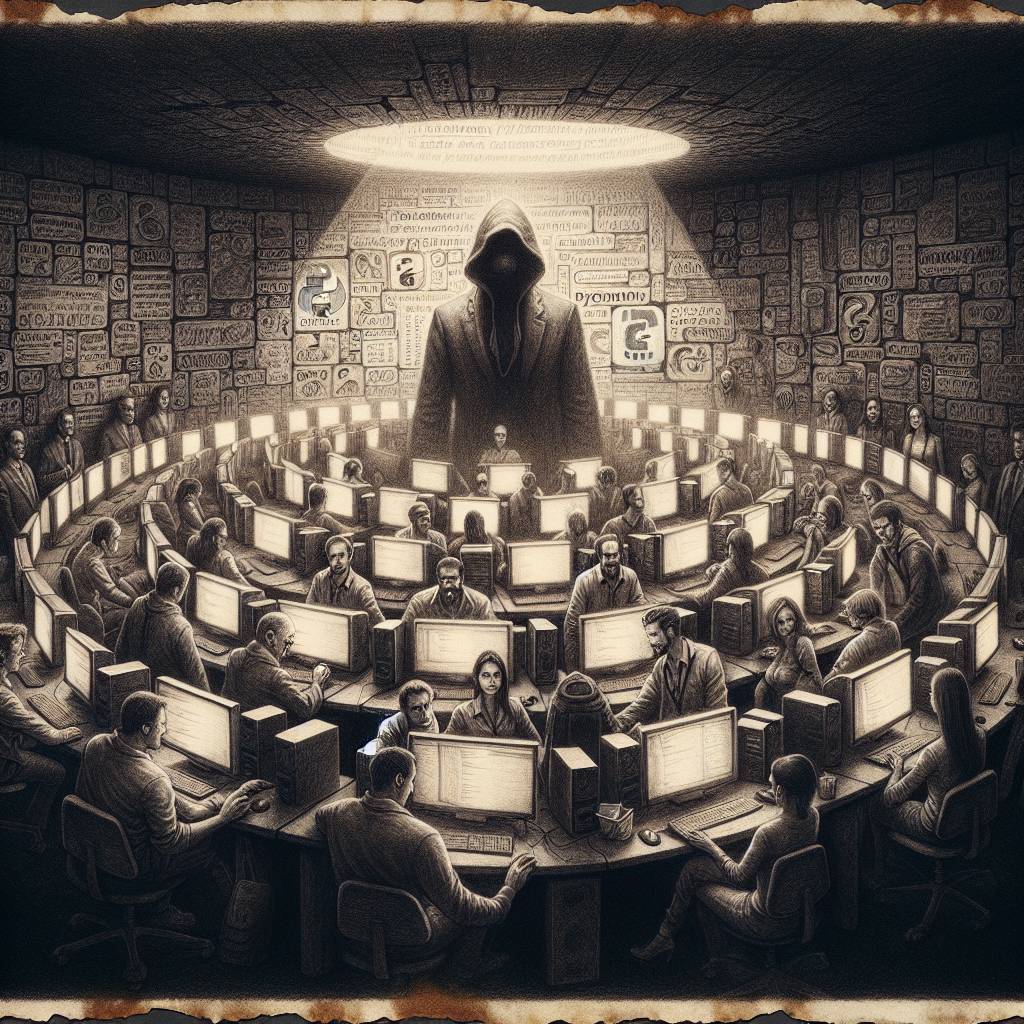
Python Phishing Fiasco: Fake PyPI Site Targets Developers with Email Scams!
Beware of phishing attacks using a fake Python Package Index website to reset credentials! The Python Software Foundation warns of emails prompting “email verification,” leading to a phishing page. Protect your PyPI account by avoiding email links, using password managers, and enabling two-factor authentication. Remember, not all packages are gifts!
Hot Take:
Looks like the Python Software Foundation is dealing with a new breed of cyber snakes, slithering their way through cyberspace with fake PyPI sites to steal credentials. Maybe it’s time for developers to brush up on their cybersecurity spells and cast a protective charm over their accounts!
Key Points:
- Phishing attacks using a fake PyPI website are targeting Python developers.
- The phishing emails prompt users to verify their email under the guise of security procedures.
- Threat actors aim to steal credentials to publish or compromise Python packages with malware.
- Developers are advised to use password managers and two-factor authentication for added security.
- The Python Software Foundation recently invalidated stolen tokens from a separate supply chain attack.
Already a member? Log in here
