Pro-Russian Hacktivists Fool Themselves: Honeypot Hijinks Unmask Cyber Blunders
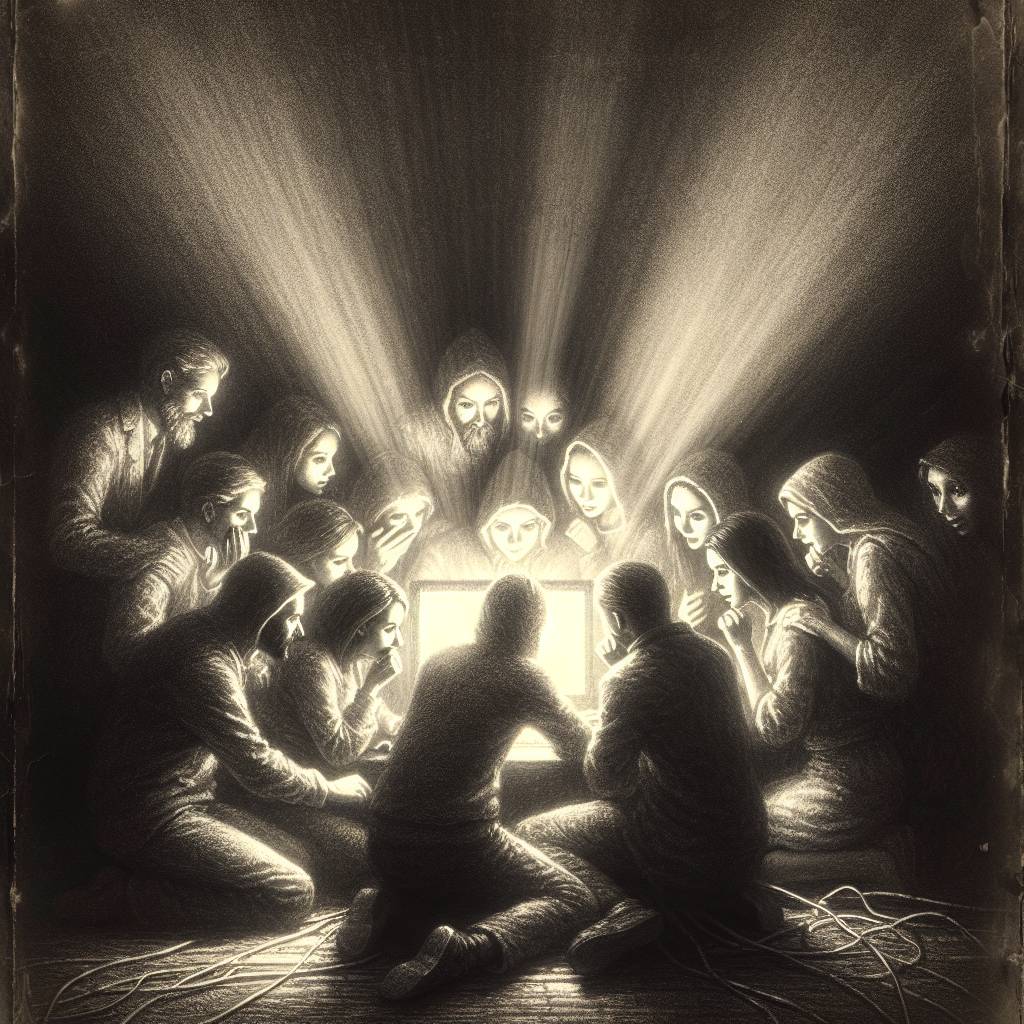
Pro-Russian hacktivist group TwoNet, famous for launching DDoS attacks, was duped by a fake water treatment plant set up by researchers. Their 26-hour escapade saw them hacking decoy systems, thinking they were causing chaos. Forescout advises bolstering security to keep such cyber mischief at bay.
Hot Take:
TwoNet’s pivot from DDoS attacks to hacking fake water plants is the cybersecurity equivalent of trying to rob a bank and finding out it’s a movie set. Too bad for them, but at least they’re keeping the cybersecurity researchers entertained. Here’s hoping they don’t stumble upon the real deal anytime soon!
Key Points:
- TwoNet, a pro-Russian hacktivist group, transitioned from DDoS attacks to targeting critical infrastructure.
- The group claimed to have hacked a water treatment facility, which was actually a honeypot set up by researchers.
- Researchers at Forescout observed the hackers gaining access using default credentials and performing disruptive actions.
- The hacktivists focused on web application vulnerabilities without attempting privilege escalation.
- Forescout suggests strong authentication and network segmentation to protect critical infrastructure.
Already a member? Log in here
