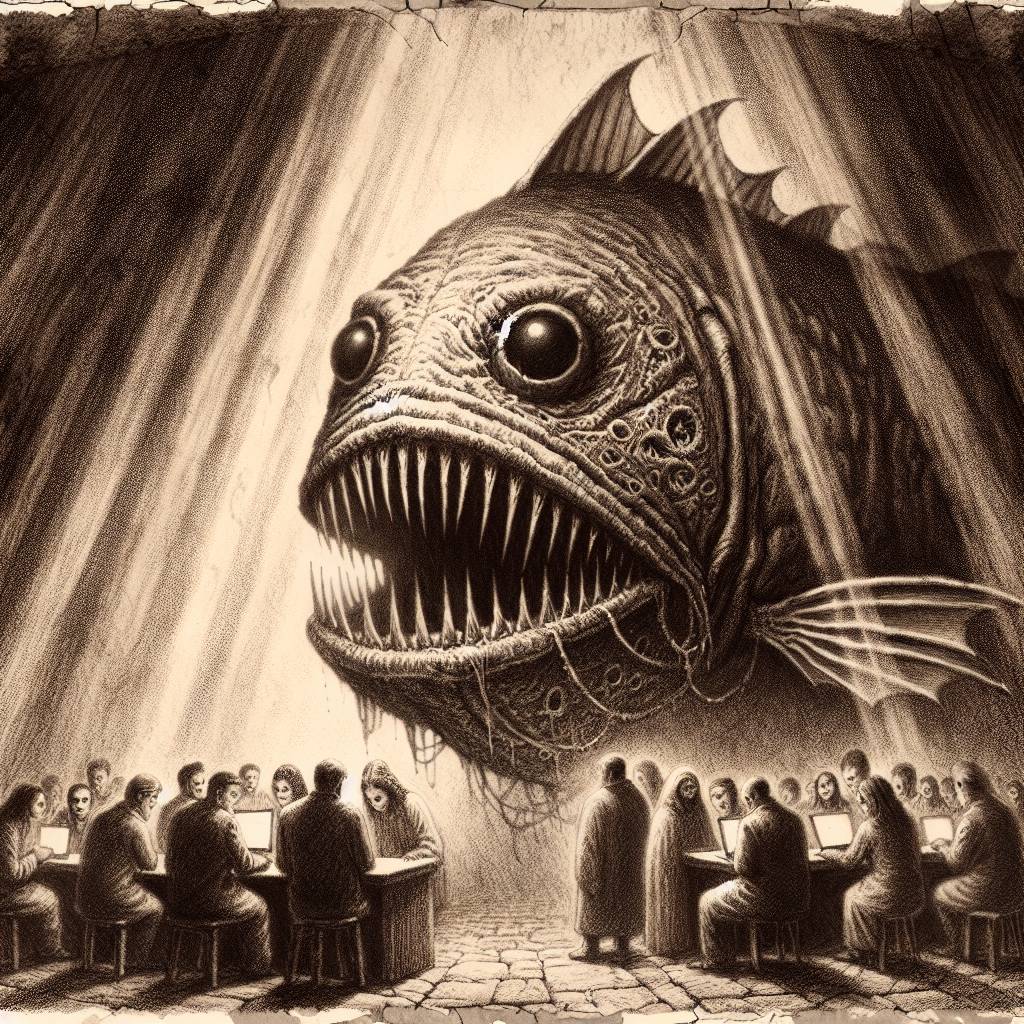
Phishy PyPI Plot: Beware of Fake Email Verification Scams!
Phishing alert! The Python Package Index (PyPI) warns users of a sly phishing attack impersonating their site. Emails trick users with a fake “Email verification” request. Beware of the rogue domain pypj.org. Always double-check URLs and never click suspicious links. If you’ve been duped, change your PyPI password pronto!
Hot Take:
Looks like hackers are getting their PhD in Phishing! The PyPI phishing attack is like a bad sequel to “You’ve Got Mail,” where the only thing you’ve got is a scam. If only hackers used their tech skills for good, we could have flying cars by now!
Key Points:
- PyPI users are targeted in a phishing attack via emails from a fake domain “pypj[.]org”.
- The attack redirects users to a fake PyPI site to steal credentials.
- The phishing site cleverly forwards credentials to the real PyPI site to avoid suspicion.
- Users are advised to verify URLs and use tools like password managers for security.
- Similar tactics have been used in previous npm attacks, hinting at a pattern.
Already a member? Log in here
