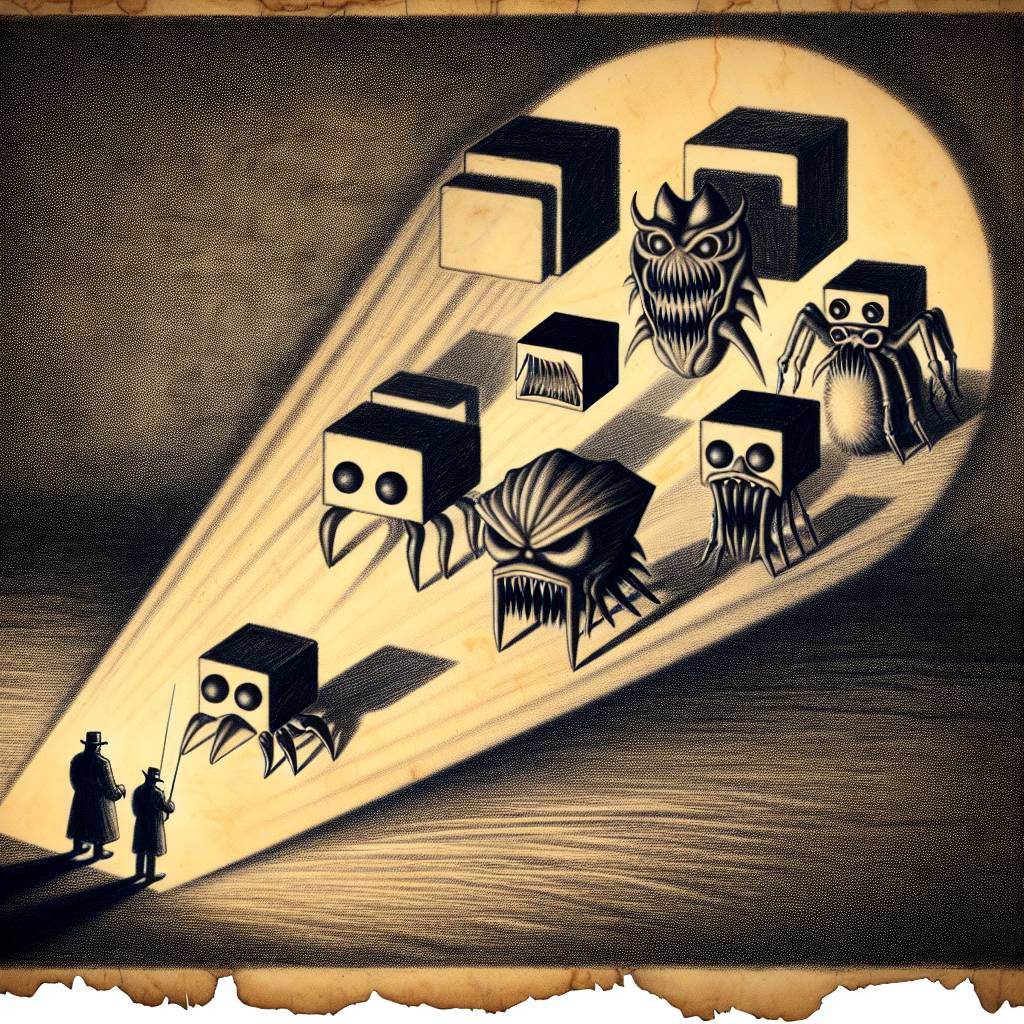
Phishy Business: Popular JavaScript Libraries Turned Malware Machines!
JavaScript libraries eslint-config-prettier and eslint-plugin-prettier were hijacked in a phishing attack. Malicious versions included a sneaky postinstall script that targeted Windows machines. Developers, avoid versions 8.10.1, 9.1.1, 10.1.6, and 10.1.7, lest you want your code to moonlight as a malware delivery service.
Hot Take:
Move over, cat phishing scams, there’s a new sheriff in town! This time, it’s a JavaScript library phishing attack, and it’s got more drama than a reality TV show. Now, developers have to add ’email skepticism’ to their skillset alongside JavaScript mastery. Who knew inboxes could be so treacherous?
Key Points:
- Popular JavaScript libraries hijacked via a targeted phishing attack.
- Malicious versions of eslint-config-prettier and eslint-plugin-prettier were published.
- The attack involved stolen credentials and unauthorized package releases.
- A postinstall script executed a trojan DLL on Windows systems.
- Developers advised to avoid specific package versions and check for compromises.
Already a member? Log in here
