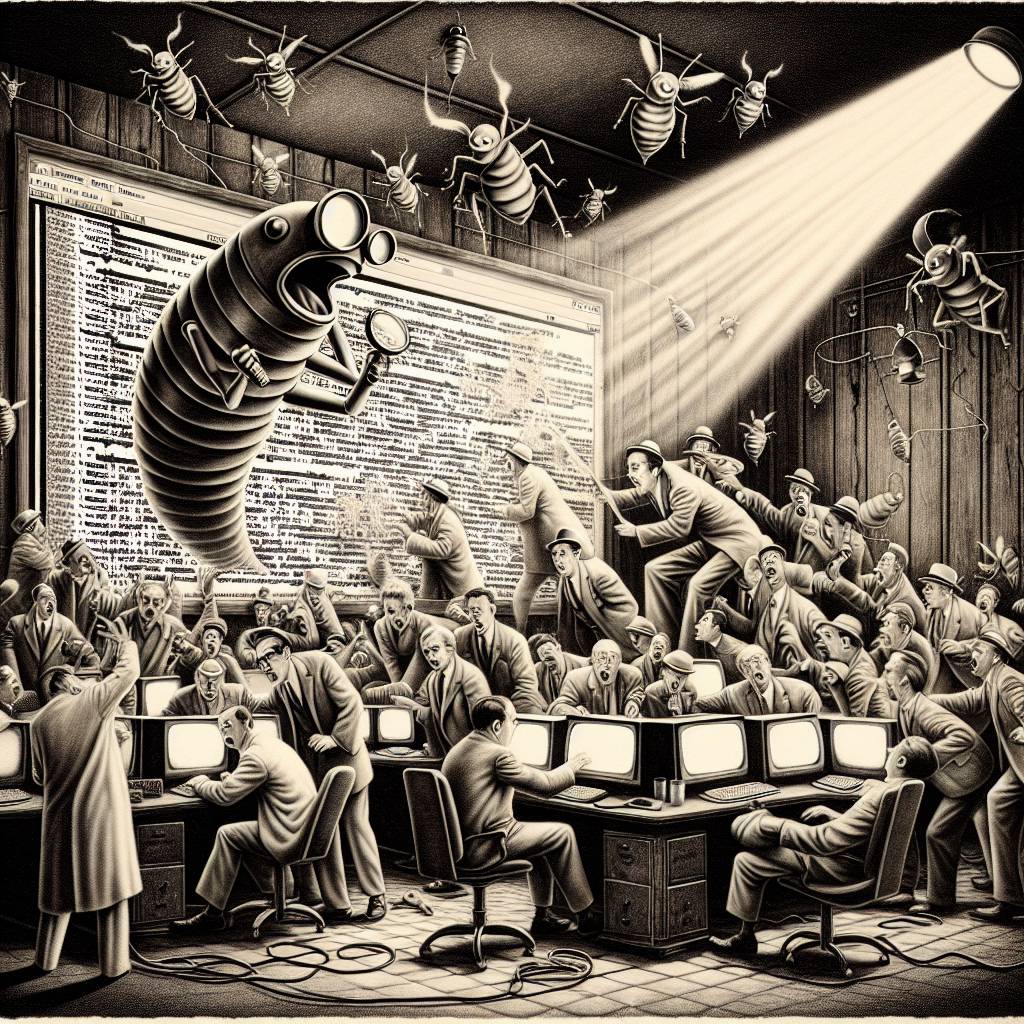
Microsoft’s “Not My Fault” Approach to .NET Flaw: A Comedy of Errors in Enterprise Security
A .NET security flaw allows attackers to manipulate SoapHttpClientProtocol, potentially enabling remote code execution. Despite researchers highlighting the issue, Microsoft insists the fault lies with developers accepting untrusted inputs. WatchTowr’s Piotr Bazydło describes the situation as a “feature, not a bug” with a dash of irony.
Hot Take:
Microsoft’s response to a .NET security flaw is like telling a driver to dodge potholes instead of fixing the road! They’ve decided it’s not a bug, it’s a feature—because who doesn’t want a surprise file write on their system? WatchTowr’s Piotr Bazydło might need to brush up on his ‘telepathy’ skills since apparently, devs are supposed to just ‘know’ these things. Talk about passing the buck!
Key Points:
- Security flaw in .NET framework affects enterprise-grade products.
- Microsoft refuses to fix, citing developer responsibility.
- Vulnerability involves manipulation of SOAP messages.
- WatchTowr identifies Barracuda Service Center as vulnerable.
- Remote code execution possible through WSDL file exploitation.
Already a member? Log in here
