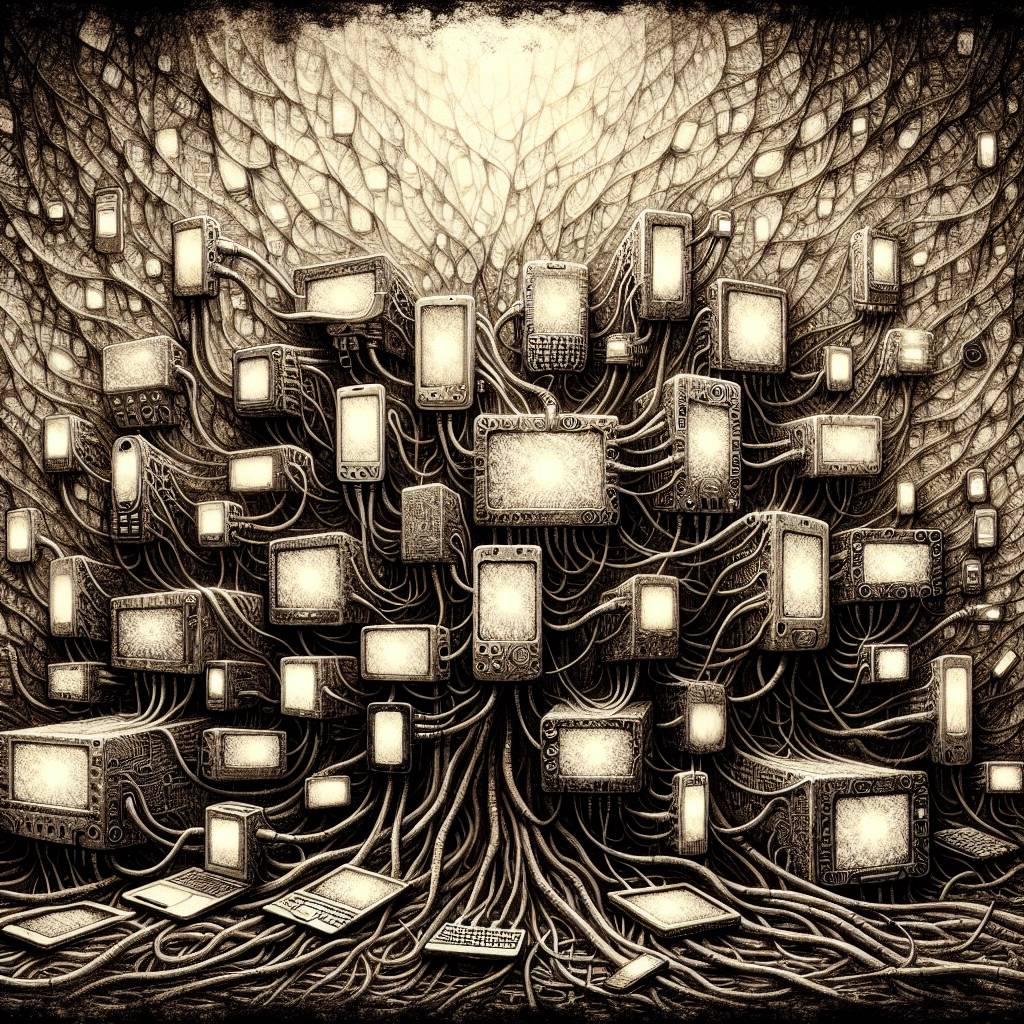
Malware Madness: Infected Devices Turned Into Proxy Playground for Cybercriminals
Infected devices turn into unwitting participants in a proxy-for-rent service, offering anonymity to anyone savvy enough to find the right IP and port. Despite efforts by Lumen and law enforcement to disrupt this operation, the abundance of vulnerable devices ensures the persistence of these threats, with only 10% of proxies flagged as malicious.
Hot Take:
When your device becomes a proxy-for-rent service, it’s like turning your home into an Airbnb without knowing. Congratulations, you’re now an unwitting host for cybercriminals worldwide! Who needs a side hustle when your gadgets are making money for someone else?
Key Points:
- Infected devices are turned into proxies-for-rent, offering anonymous traffic routing.
- No authentication is required, leaving devices vulnerable to anyone who finds the right IP and port.
- Only a small percentage of these proxies are flagged as malicious by detection tools.
- Lumen and law enforcement partners have disrupted part of the network, but many vulnerable devices remain.
- Security experts advise monitoring, blocking open proxies, and updating outdated devices.
Already a member? Log in here
