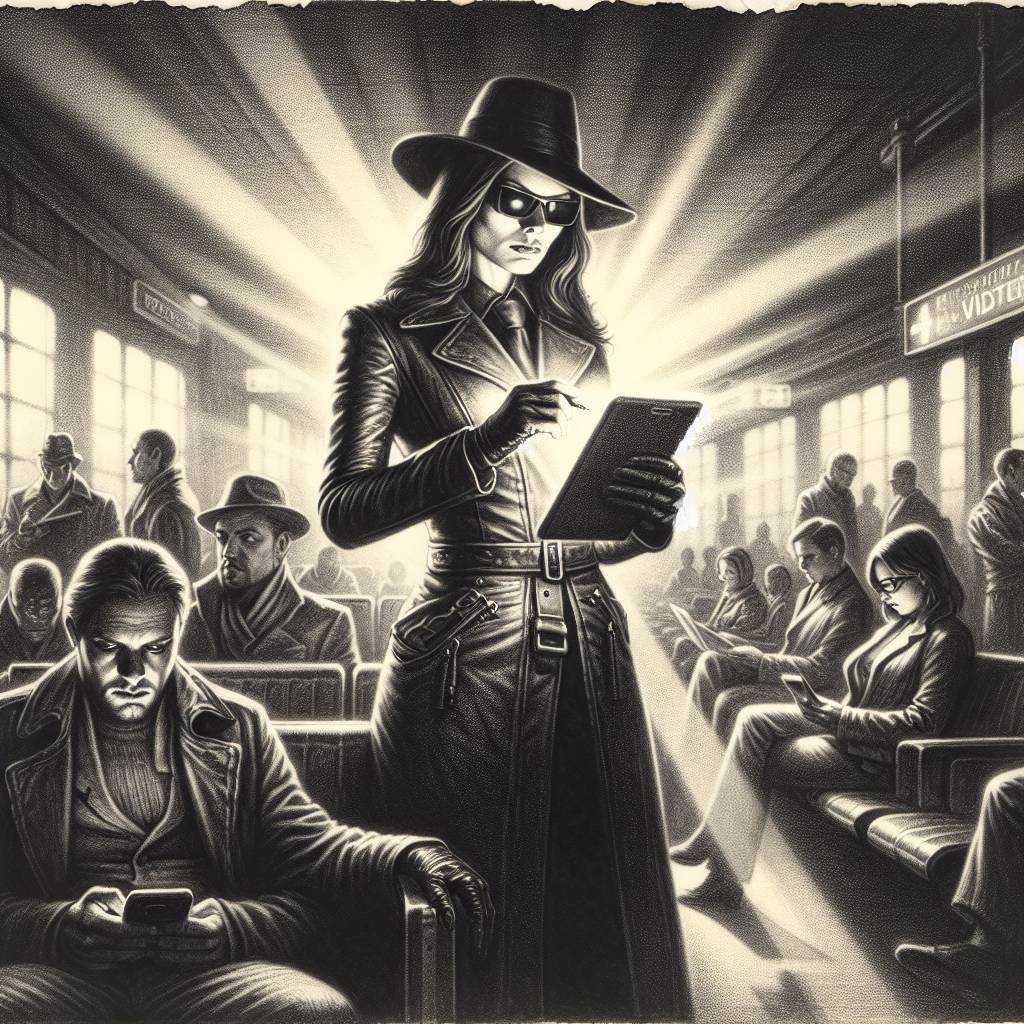
LightPerlGirl Strikes: New ClickFix Variant Targets Tech-Savvy Travelers! 🚨✈️
Researchers at Todyl have unearthed a sneaky ClickFix variant, LightPerlGirl, that uses PowerShell to sneak malware past unsuspecting users. The devious plot involves tricking vacation-seekers on a compromised travel site into executing code, potentially leading to major enterprise breaches. Talk about a trip to the Galapagos turning into a digital disaster!
Hot Take:
Wow, LightPerlGirl sounds like a name for a quirky superhero, but instead of saving the day, she steals your data while you’re dreaming of sipping cocktails on the Galapagos Islands! Who knew booking a vacation could turn into a cybersecurity horror story?
Key Points:
- Researchers at Todyl discovered a new ClickFix variant named LightPerlGirl.
- The malware utilizes social engineering to execute PowerShell commands via LOLBINS.
- It was found on a compromised WordPress travel site used in a waterholing attack.
- The malware delivers Lumma infostealer but its source remains unclear.
- The attack targets unsuspecting wealthy travelers seeking an exotic getaway.
Already a member? Log in here
