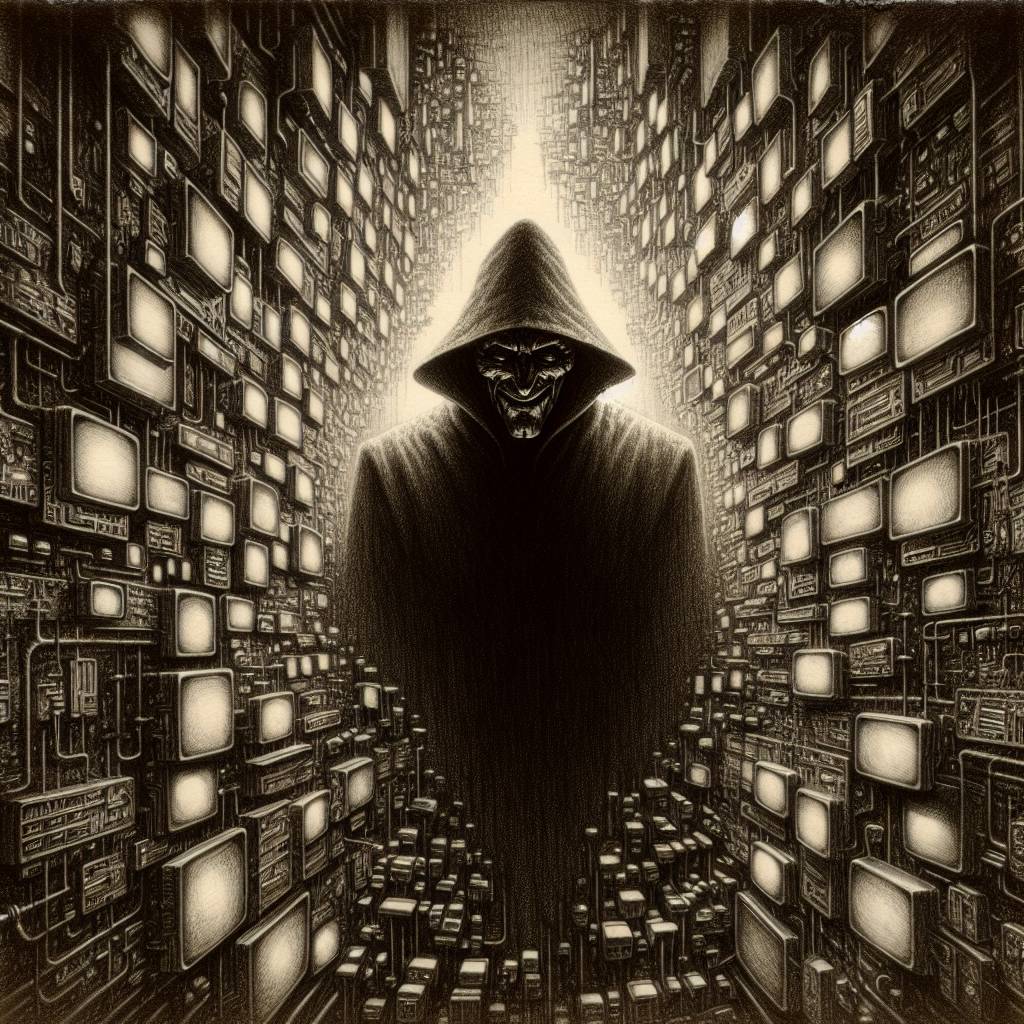
LDAP Mayhem: Unmasking Cyber Villains with Directory Detection Strategies
Need a laugh while learning about LDAP enumeration? This guide breaks down the serious business of detecting LDAP-based attacks with a sprinkle of humor. Discover how cybercriminals love LDAP for lateral movement, the challenge of spotting malicious activity, and how tools like BloodHound sniff out directory data. Stay secure and entertained!
Hot Take:
Who knew that the LDAP could be the unsung hero of IT departments and the mischievous villain of cybercriminals at the same time? It’s like LDAP is living a double life, like a secret agent with a directory full of secrets!
Key Points:
- LDAP is a key protocol for directory services but is also a favorite tool for cybercriminals.
- Distinguishing between innocent and malicious LDAP activities is as tricky as spotting Waldo at a stripes convention.
- Tools like BloodHound and SharpHound are frequently used by attackers to exploit LDAP.
- Palo Alto Networks offers solutions to help detect and mitigate LDAP-based attacks.
- Real-world examples show how attackers use LDAP enumeration in cyber campaigns.
Already a member? Log in here
