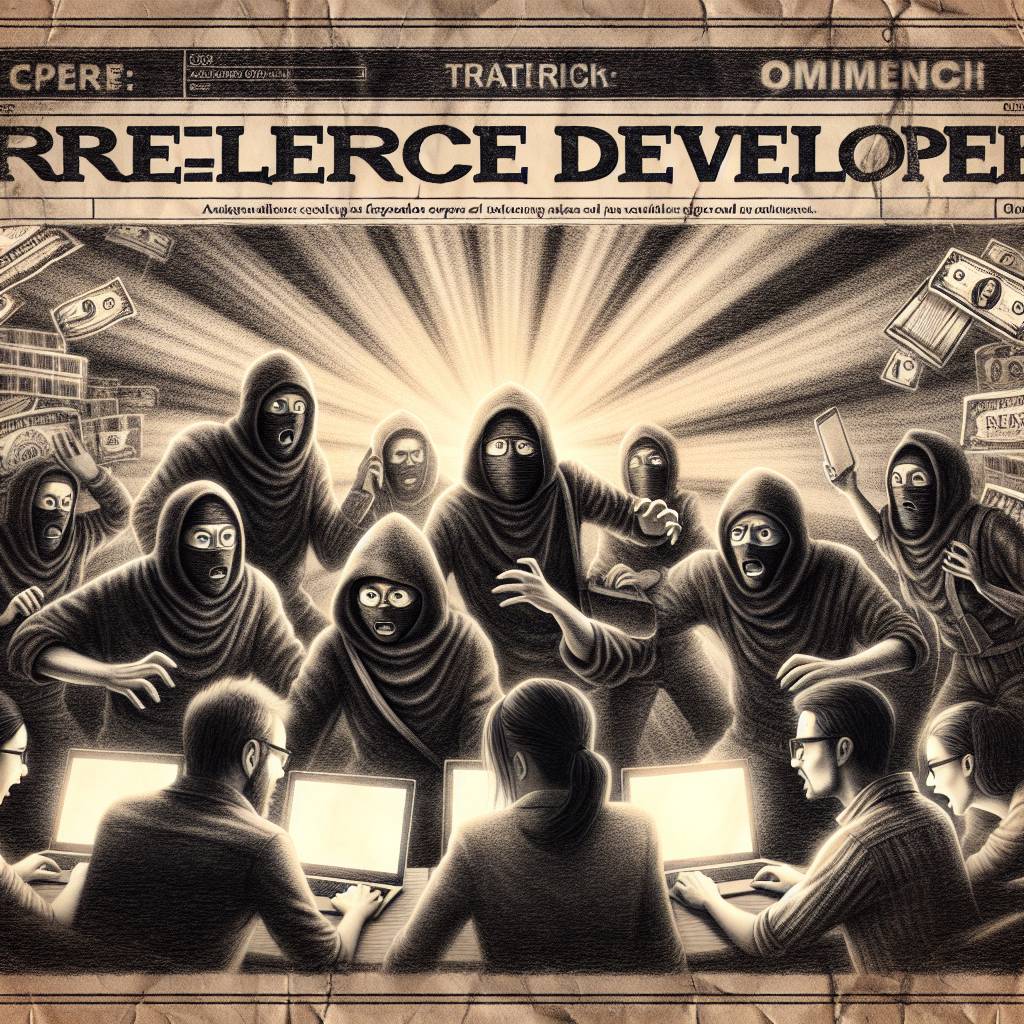
Lazarus Group’s Sneaky Attack on Freelance Developers: A Crypto Catastrophe
North Korea’s Lazarus group is targeting software developers in Operation 99, a campaign aimed at stealing sensitive data. By posing as recruiters, they trick developers into downloading malicious code. The attack marks a strategic shift in the group’s tactics, focusing on freelancers in the cryptocurrency sector. Developer caution is advised.
Hot Take:
Well, folks, looks like the Lazarus Group is back at it again, proving that when it comes to hacking, they’re not here to make friends, just make bank. Who knew North Korea had a knack for tech recruitment scams and Python scripts? Forget LinkedIn endorsements, just don’t endorse malware, okay?
Key Points:
- Lazarus Group’s “Operation 99” targets software developers to steal sensitive data and crypto keys.
- The campaign marks a shift from broad phishing attacks to targeted hits on the tech supply chain.
- Freelance developers in the cryptocurrency sector are particularly in the crosshairs.
- Operation involves fake recruiter schemes and malicious GitHub repositories.
- SecurityScorecard urges proactive security measures for developers and organizations.
Already a member? Log in here
