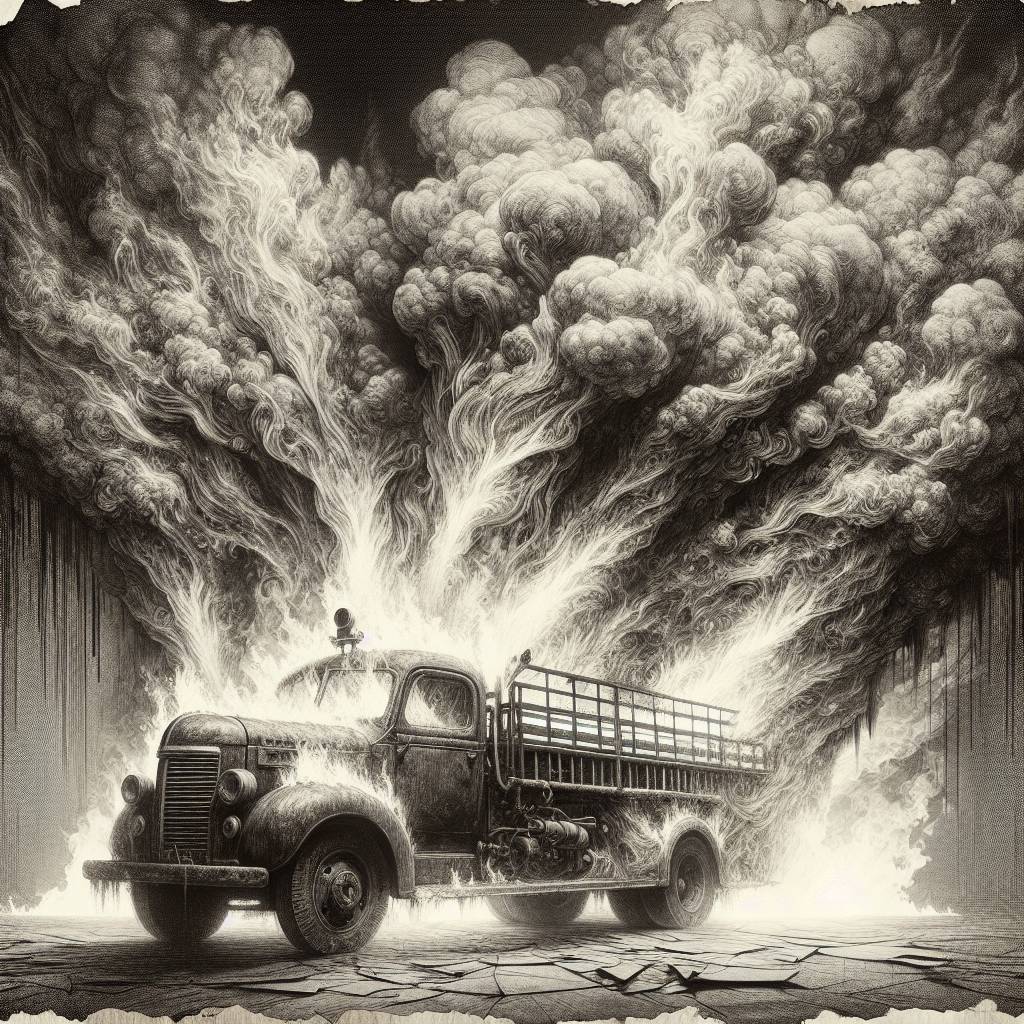
JSFireTruck Chaos: How Malicious Code is Revving Up Cyber Threats!
Cybersecurity researchers are sounding the alarm on a “large-scale campaign” involving JSFireTruck obfuscation to compromise websites with malicious JavaScript. This technique uses symbols [, ], +, $, {, and } to hide the code’s true purpose, making it a real headache—and a bit of a potty-mouthed one at that—for analysts.
Hot Take:
It seems that cybercriminals are now resorting to the equivalent of writing Shakespearean sonnets with a typewriter that only has six keys. Welcome to the world of JSFireTruck, where the only thing that’s more confusing than the code is the name it was given. Move over, JSFuck, there’s a new firetruck in town—and it’s hauling a load of malicious mischief! Watch out, or you might end up getting redirected to parts of the internet even your browser’s incognito mode hesitates to visit.
Key Points:
- Malicious JavaScript injections are compromising legitimate websites on a large scale.
- The obfuscation technique, humorously dubbed JSFireTruck, employs simple symbols to hide the code’s purpose.
- The injected code redirects users to malicious URLs if the referrer is a search engine.
- 269,552 web pages infected with JSFireTruck code between March and April 2025.
- HelloTDS is another threat that uses fake CAPTCHA pages to deploy scams and malware.
