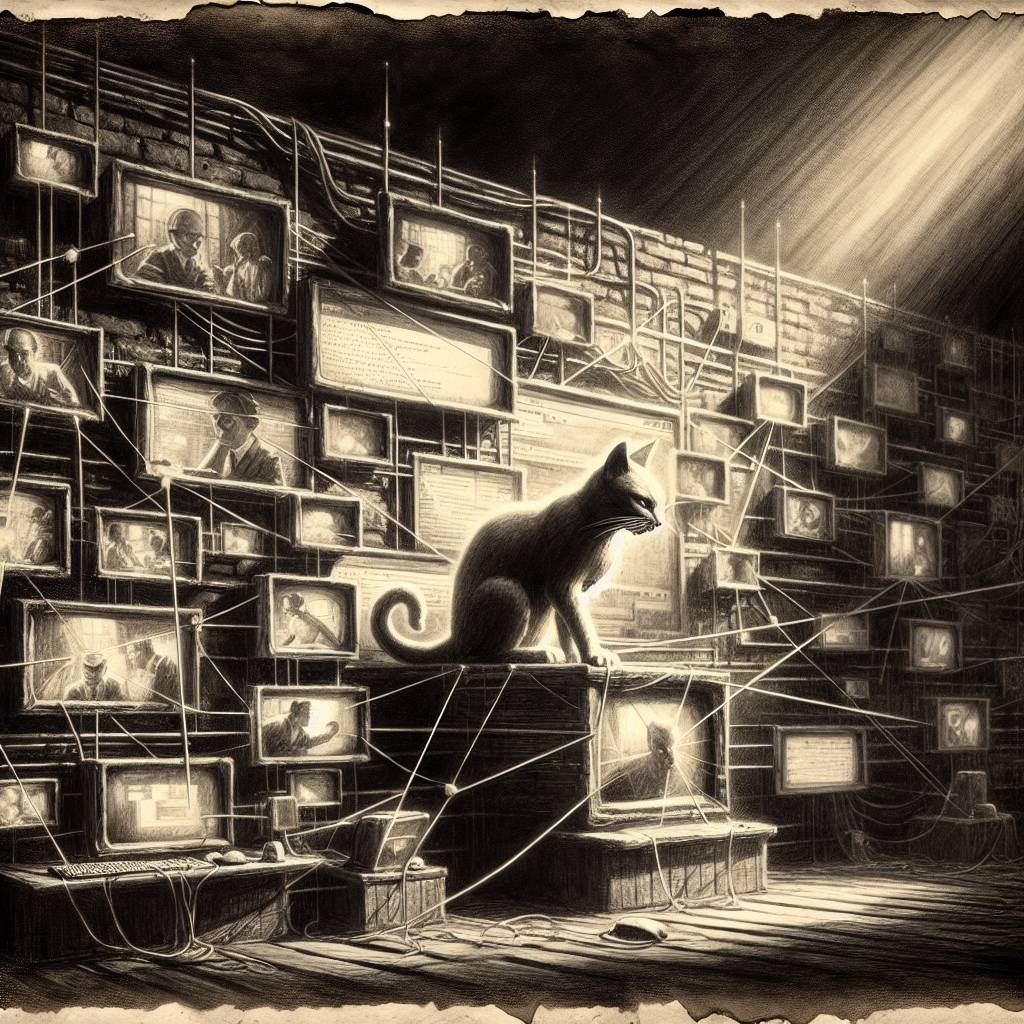
Iranian Cyber Cat-and-Mouse: BladedFeline’s Decade-Long Hide and Seek in Kurdish Networks Revealed
BladedFeline, an Iranian cyber-espionage group, managed to play hide-and-seek in a target’s network for nearly a decade before being discovered in 2023. Their high-stakes game involved strategic espionage on Kurdish and Iraqi officials, proving that when it comes to stealthy cyber tactics, these cats have nine lives and then some.
Hot Take:
Who knew that the feline family had a cyber-espionage division? BladedFeline clawed its way into networks and purred quietly for nearly a decade. Talk about a slow and steady cat-and-mouse game!
Key Points:
- BladedFeline, an Iranian APT group, has been lurking in networks since at least 2017.
- ESET identified their proprietary backdoor, “Shahmaran,” used against Kurdish officials.
- The group is suspected to be a subgroup of the infamous Oilrig, also known as APT34.
- BladedFeline targets high-ranking officials, focusing on espionage-related activities.
- They maintained stealthy access, blending into normal network traffic for years.
Already a member? Log in here
