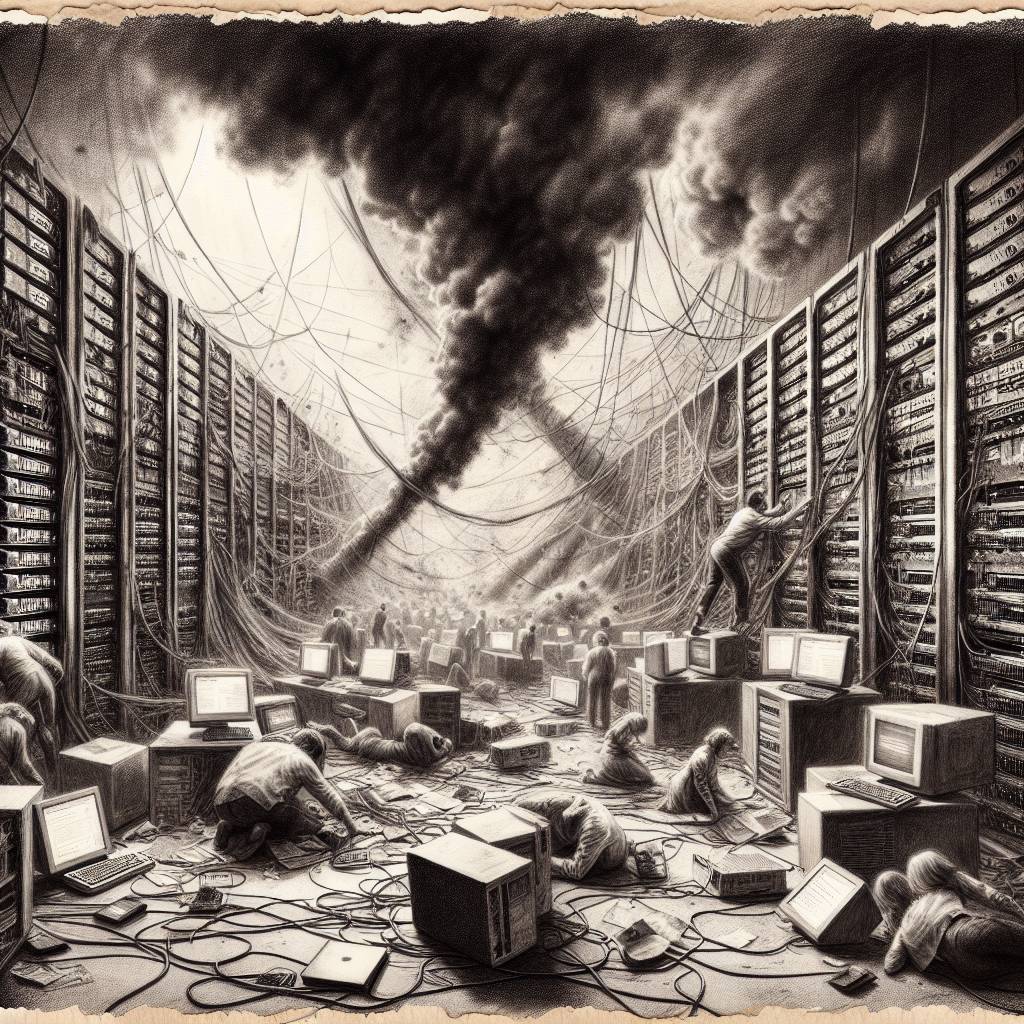
HTTP/2 Fiasco: “MadeYouReset” Bug Unleashes Chaos on Web Servers!
Security researchers have uncovered a common design flaw in HTTP/2, dubbed “MadeYouReset,” which could lead to massive denial-of-service attacks. This flaw affects many major vendors, including Google, IBM, and Microsoft, requiring coordinated disclosure. So, if your server suddenly takes a nap, don’t blame it—blame HTTP/2’s bug-filled fiesta!
Hot Take:
HTTP/2 had one job: make the web faster and better. Instead, it’s become the digital equivalent of leaving your front door unlocked with a neon sign saying “Come on in, hackers!” Researchers have found a way to make servers go from speedy to snoozy in seconds, proving once again that with great power comes great responsibility—for patching vulnerabilities.
Key Points:
- HTTP/2, despite being a decade old, is still vulnerable to massive Denial of Service (DoS) attacks.
- The “MadeYouReset” flaw allows attackers to bypass HTTP/2’s concurrency limits.
- The flaw is related to the earlier “Rapid Reset” vulnerability from 2023.
- Over 100 vendors, including tech giants like Google, IBM, and Microsoft, are affected.
- Mitigation strategies include stricter protocol validation and anomaly detection systems.
Already a member? Log in here
