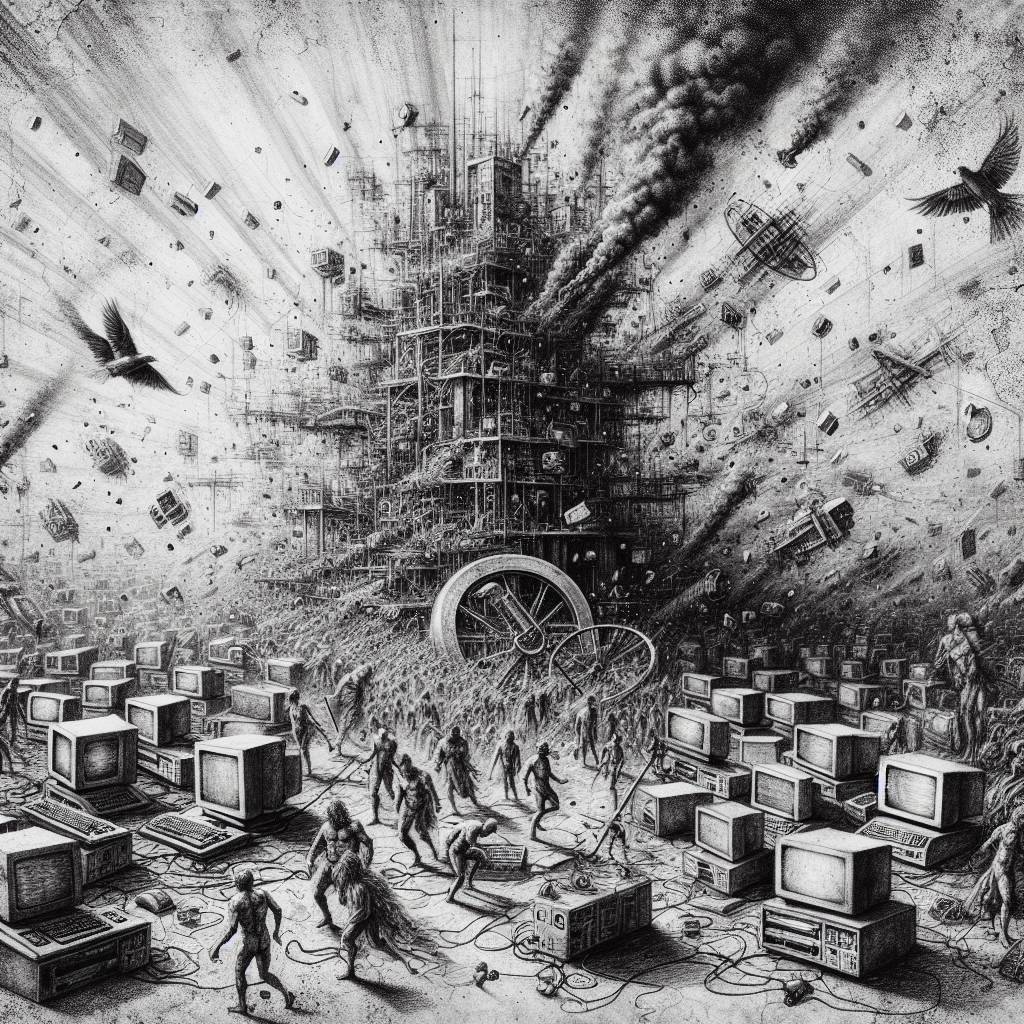
Hackers Unleash Auto-Color Malware: SAP NetWeaver Exploit Chaos!
Hackers are dancing the tango with a critical SAP NetWeaver vulnerability, CVE-2025-31324, deploying Auto-Color Linux malware faster than a cat meme goes viral. Darktrace found the malware now sports advanced evasion tactics, making it sneakier than a ninja in a library. If you’re running NetWeaver, update faster than you can say “cyberattack”!
Hot Take:
It seems like Auto-Color is painting the town red, or at least the server rooms, with its latest antics! Who knew hackers could be such art enthusiasts, turning vulnerabilities into their canvas for chaos? But seriously, SAP NetWeaver users, it’s time to get those updates rolling faster than you can say ‘CVE-2025-31324’ before your databases end up with more holes than a cheese grater!
Key Points:
- The Auto-Color malware is exploiting a critical SAP NetWeaver vulnerability, CVE-2025-31324.
- Darktrace identified an attack on a U.S. chemicals company, with hackers employing advanced evasion tactics.
- The malware’s bag of tricks includes command execution, file modification, reverse shell access, and more.
- Auto-Color adapts based on user privilege level and uses stealthy tactics like ‘ld.so.preload’ for persistence.
- SAP has released a patch, but exploitation attempts by ransomware actors and state hackers are ongoing.
Already a member? Log in here
