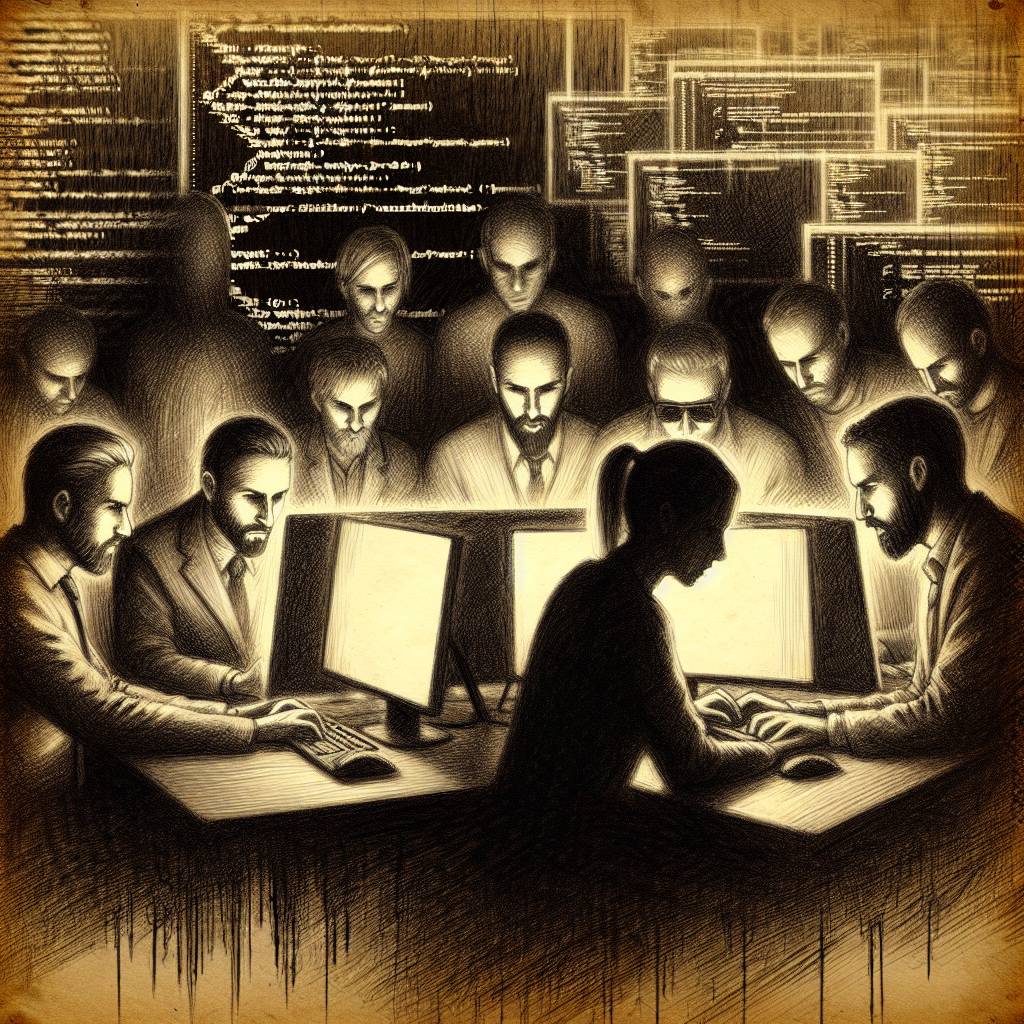
Hackers Run Amok: OttoKit WordPress Plugin Vulnerability Creates Admin Chaos!
Hackers are on the loose, exploiting the OttoKit WordPress plugin to create rogue admin accounts. A critical privilege escalation vulnerability lets attackers bypass authentication and party in your admin panel. Update now or face the chaos of unauthorized admin accounts sporting random usernames and passwords. OttoKit users, secure your sites pronto!
Hot Take:
Oh, WordPress, the gift that keeps on giving… to hackers. Yet again, a plugin, OttoKit, is in the spotlight for its starring role as the unwitting accomplice in a privilege escalation drama. It’s like an unending episode of “How I Met Your Administrator Account”! One moment you’re automating workflows, the next you’re automating hacker access to your website. Time to patch faster than a caffeine-fueled squirrel on rollerblades!
Key Points:
- OttoKit, a WordPress plugin, had a critical vulnerability allowing admin account creation.
- The vulnerability, CVE-2025-27007, was due to a logic error in the API function.
- Patch was released on April 21, 2025, but exploitation began 90 minutes post-disclosure.
- Hackers used REST API endpoints to create rogue admin accounts silently.
- It’s the second such flaw in OttoKit since April 2025, both leading to unauthorized admin access.
