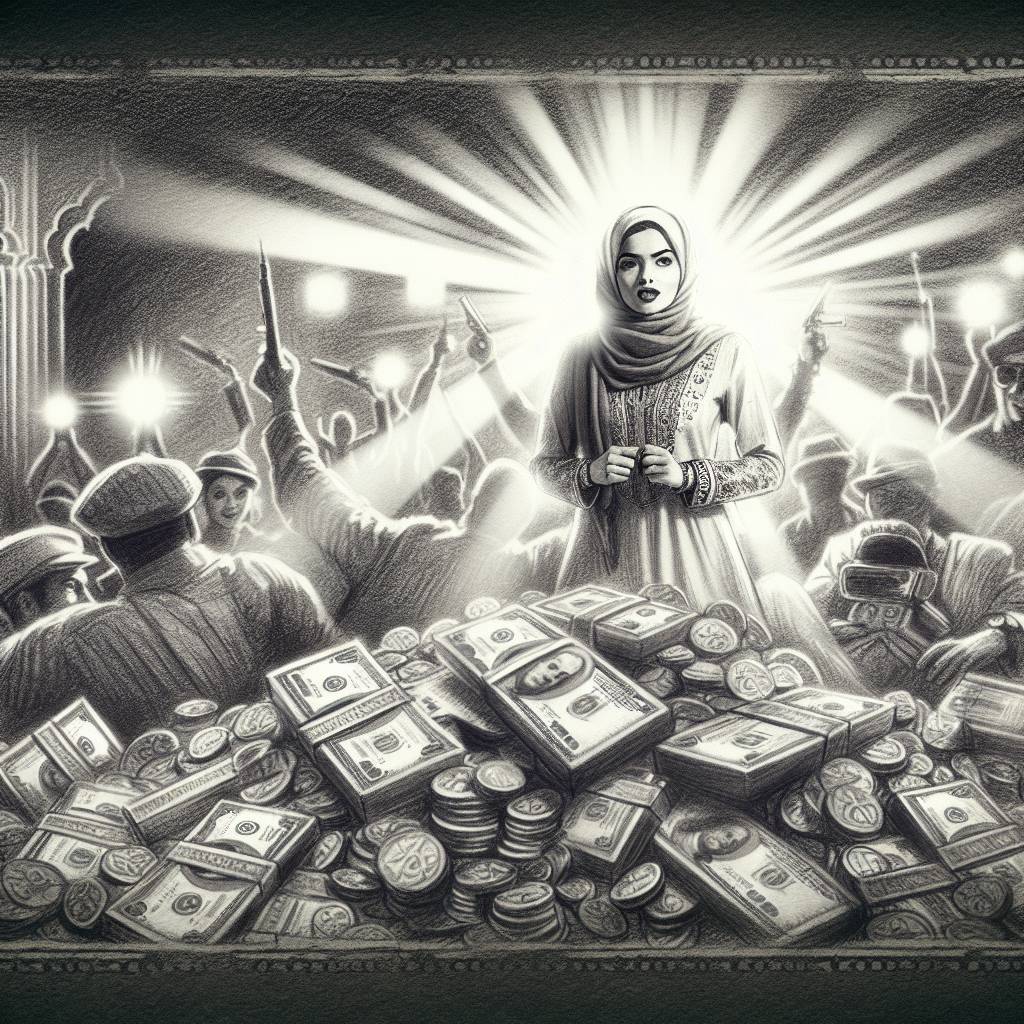
Google’s $12M Bug Bounty Bonanza: Cashing In on Cyber Sleuths!
In 2024, Google paid almost $12 million in bug bounty rewards to 660 researchers through its Vulnerability Reward Program. With rewards now reaching up to $450,000 for top-quality reports, Google’s bug bounty blitz leaves no bug unturned and no wallet empty. Cheers to making software safer, one vulnerability at a time!
Hot Take:
Google’s bug bounty program is like the Oscars of cybersecurity, except instead of golden statues, you get a big fat check, and instead of paparazzi, you have hackers trying to crash your party. This year, Google shelled out nearly $12 million to sleuths who found more bugs than an entomologist at a picnic. It’s time to celebrate the unsung heroes who make the internet a less terrifying place—one bug at a time!
Key Points:
- Google’s Vulnerability Reward Program (VRP) rewarded $12 million to 660 researchers in 2024.
- The program increased the maximum reward for critical vulnerabilities to $151,515, with some reports fetching up to $450,000 in the Mobile VRP.
- Chrome and Cloud VRP saw significant increases in bounty rewards, with Chrome payouts exceeding $250,000.
- A new program, kvmCTF, was launched, offering $250,000 for exploits targeting the KVM hypervisor.
- Google has awarded $65 million in bug bounties since the VRP’s inception in 2010.
Already a member? Log in here
