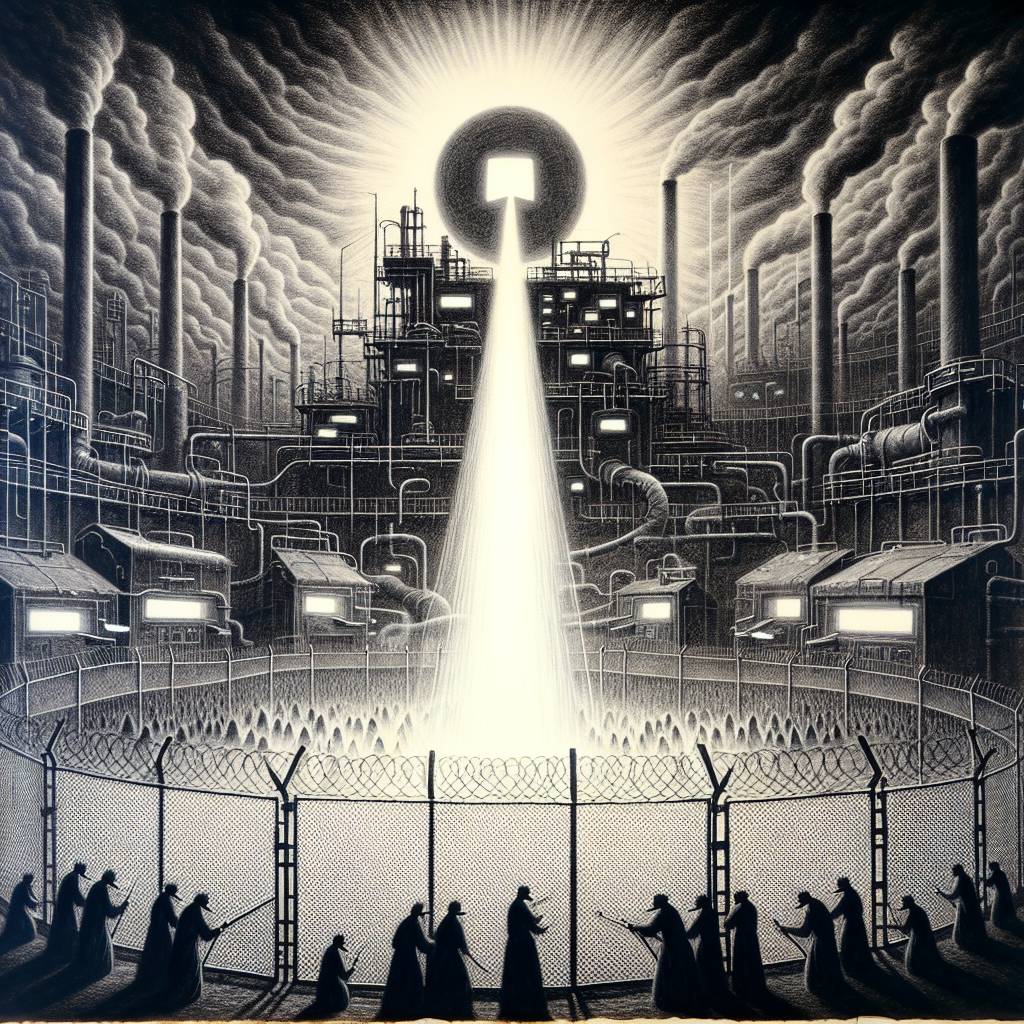
GitHub Supply Chain Fiasco: Stolen Token Turns 23,000 Repos into Secret-Leaking Machines!
The massive GitHub supply chain attack that spilled secrets from 23,000 projects all started with a stolen token from a SpotBugs workflow. The attackers used this token to tamper with the popular tj-actions/changed-files GitHub Action, quietly stashing developers’ secrets in log files. Who knew stealing secrets could be so… open source?
Hot Take:
Who knew that a ‘Spot’ of bad luck could lead to such ‘Bug’-tacular chaos? It looks like the cybersecurity world has found its new favorite detective story, starring a stolen token, a suspicious pull request, and more secrets than a teen drama. GitHub’s got some splainin’ to do!
Key Points:
- GitHub supply chain attack traced back to a leaked token from SpotBugs.
- Attackers used the token to compromise tj-actions/changed-files GitHub Action.
- Over 23,000 GitHub repositories potentially leaked secrets due to the tampering.
- Attack began in November 2024, earlier than initially suspected.
- Investigations by Unit 42 suggest a complex, multi-stage attack plan.
Already a member? Log in here
