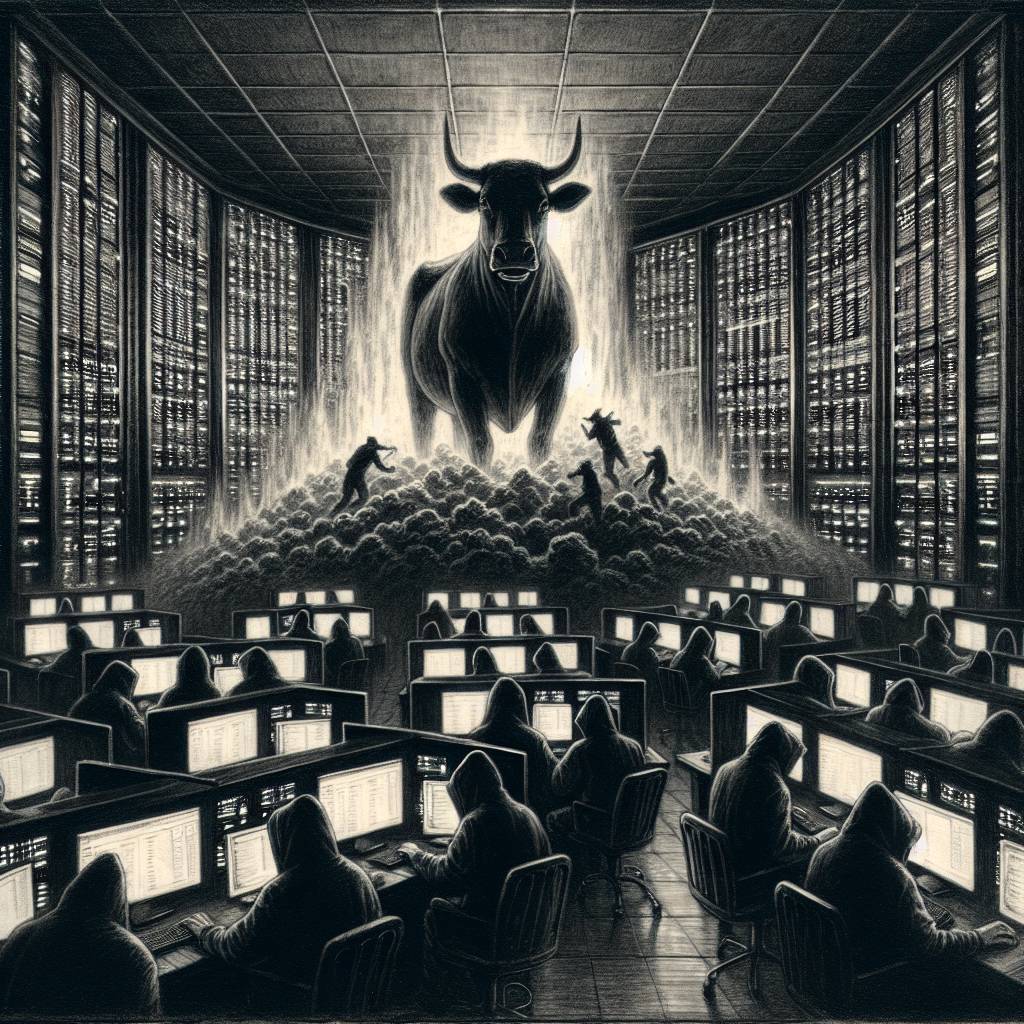
GeoServer Exploit Comedy: When Hackers Turn Bandwidth into Cash Cow Catastrophe
Watch out, folks! Cybercriminals are targeting the GeoServer database’s CVE-2024-36401 vulnerability with a CVSS score of 9.8. Their goal? To hijack your bandwidth for passive income using sneaky SDKs and apps. It’s like a bad roommate freeloading on your WiFi! Protect yourself and stay informed against these stealthy digital squatters.
Hot Take:
Looks like cybercriminals are taking a page from the freeloading playbook of app developers, transforming your bandwidth into their personal ATM. Who knew that the dark web was just one GeoServer exploit away from becoming their own version of Netflix and chill?
Key Points:
- CVE-2024-36401 in GeoServer is exploited for remote code execution.
- Attackers monetize compromised systems by sharing victim’s bandwidth.
- Campaign started in March 2025 and continues to evolve with shifting tactics.
- The exploitation method mimics legitimate passive income SDKs.
- Palo Alto Networks offers multiple products to thwart these threats.
Already a member? Log in here
