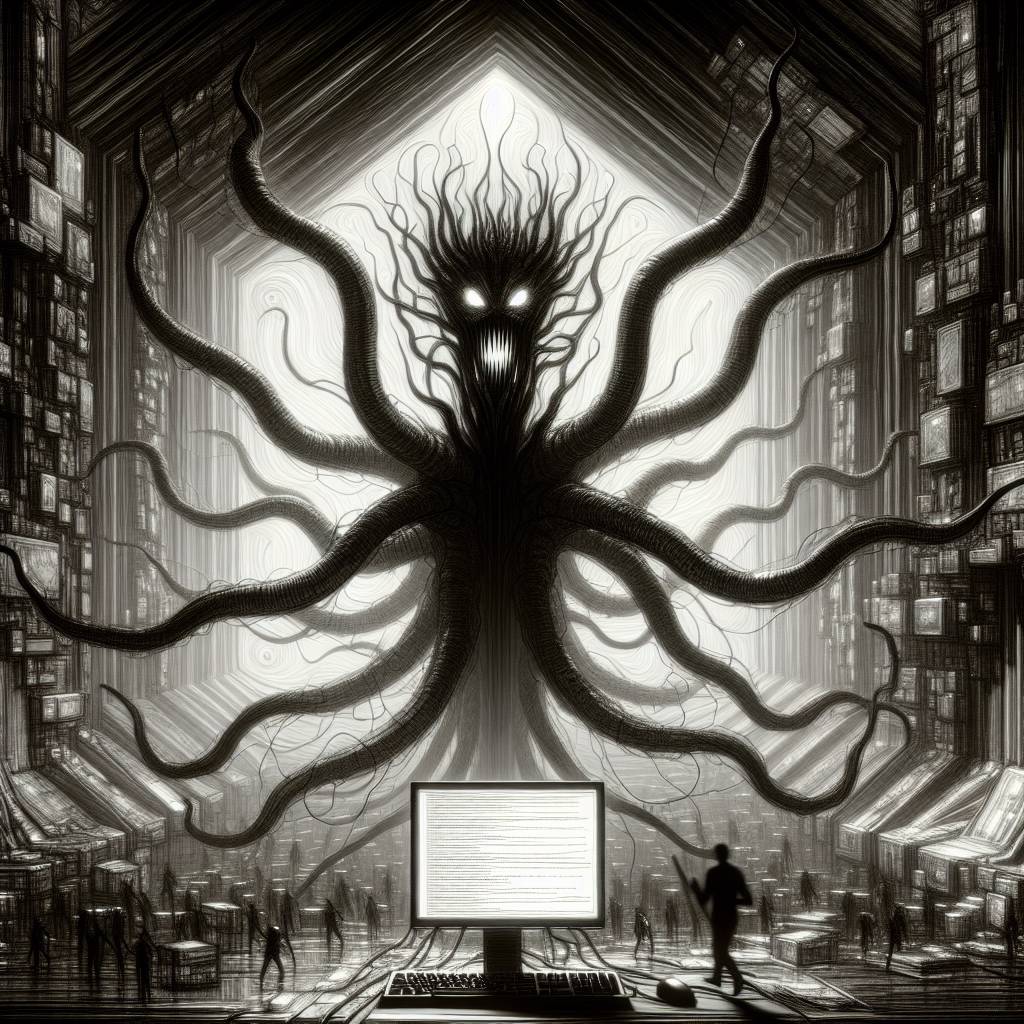
Game Over: GodLoader Malware Levels Up with Godot Engine Exploit
Hackers have deployed GodLoader malware, exploiting the Godot game engine to evade detection and infect over 17,000 systems. Utilizing Godot’s GDScript language, they bypass security systems, executing malicious code. This has led to credential theft and crypto mining, with the Stargazers Ghost Network disguising their activities via GitHub repositories.
Hot Take:
Godot, the beloved open-source game engine, has just been awarded the “Most Unwanted Malware Host” of the year! Who knew game development could be this thrillingly dangerous? Forget leveling up your character, now it’s all about leveling up your antivirus software.
Key Points:
- GodLoader malware exploits the Godot game engine to infect over 17,000 systems in three months.
- The malware uses Godot’s GDScript scripting language to execute malicious code unnoticed.
- GodLoader distributes malware through the Stargazers Ghost Network, a DaaS platform.
- Stargazer Goblin, the mastermind behind the attacks, has been active since at least August 2022.
- GodLoader targets gamers and developers across multiple platforms, including Windows, macOS, and Linux.
Already a member? Log in here
