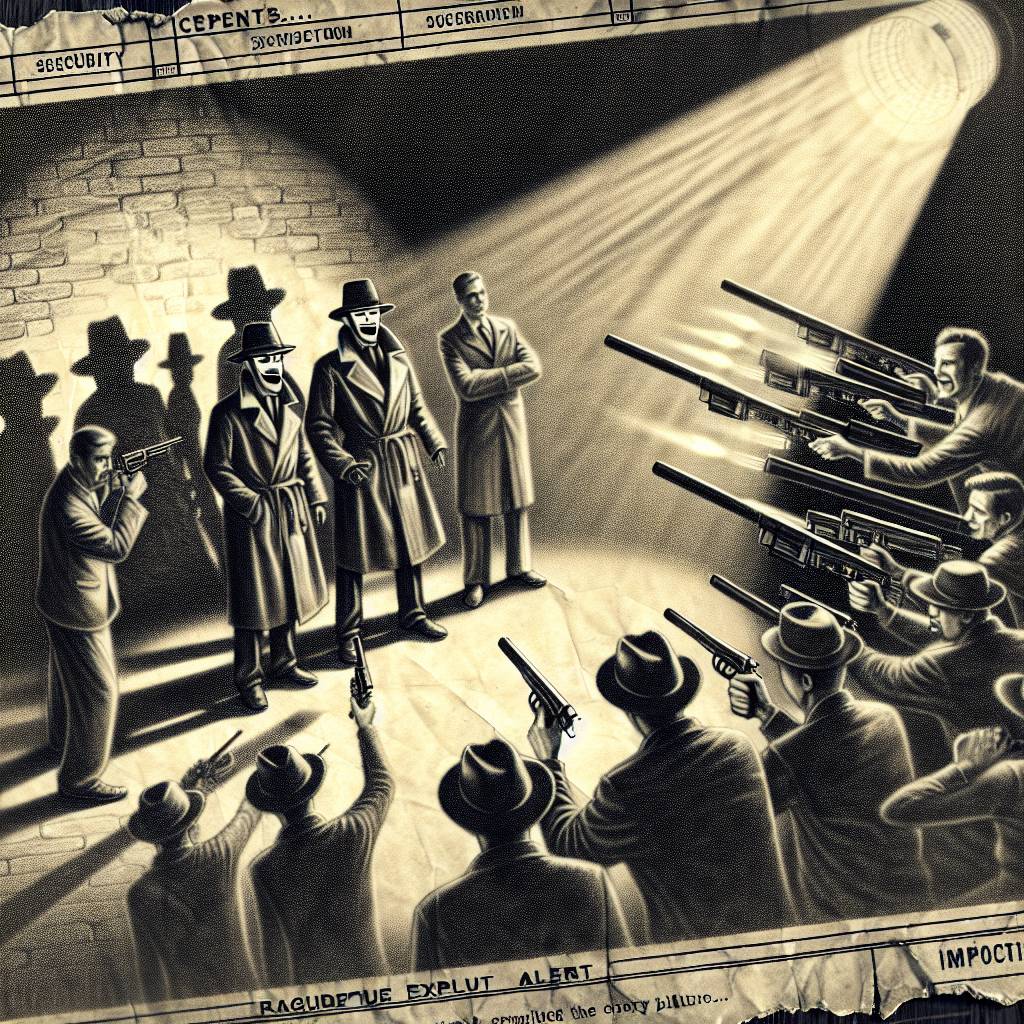
Fake Exploit Alert: Cyber Tricksters Target Security Gurus with Malware Bait!
Threat actors have created a fake proof-of-concept exploit for a critical Microsoft vulnerability, luring security researchers into downloading malware. This fake PoC targets a denial-of-service vulnerability in LDAP. Researchers are urged to verify code sources and be cautious of suspicious repositories that may contain malicious content. Stay vigilant, folks!
Hot Take:
It seems like some cyber villains have decided to play the ultimate game of catfish with security researchers. Now, a fake proof-of-concept (PoC) isn’t just a nerdy prank—it’s a full-blown malware trap. The next time you see a suspiciously shiny PoC, maybe think twice before taking the bait, lest you become the unwitting star of “How to Catch a Cybersecurity Researcher.”
Key Points:
- Cybercriminals have crafted a counterfeit PoC exploit targeting a critical Microsoft vulnerability.
- This vulnerability involves Microsoft’s Windows Lightweight Directory Access Protocol (LDAP).
- The fake PoC is a Trojan horse for information-stealing malware.
- It exfiltrates sensitive data like computer specs, network details, and installed updates.
- Trend Micro advises researchers to stick to reputable sources and review repository details diligently.
Already a member? Log in here
