Erlang RCE Vulnerability: A Comedy of Errors with Critical Consequences!
A severe remote code execution vulnerability in Erlang’s Open Telecom Platform is causing a stir. This digital mischief-maker, CVE-2025-32433, lets attackers bypass the bouncer and wreak havoc. With hackers on the prowl, experts suggest patching faster than you can say “Erlang/OTP.”
Hot Take:
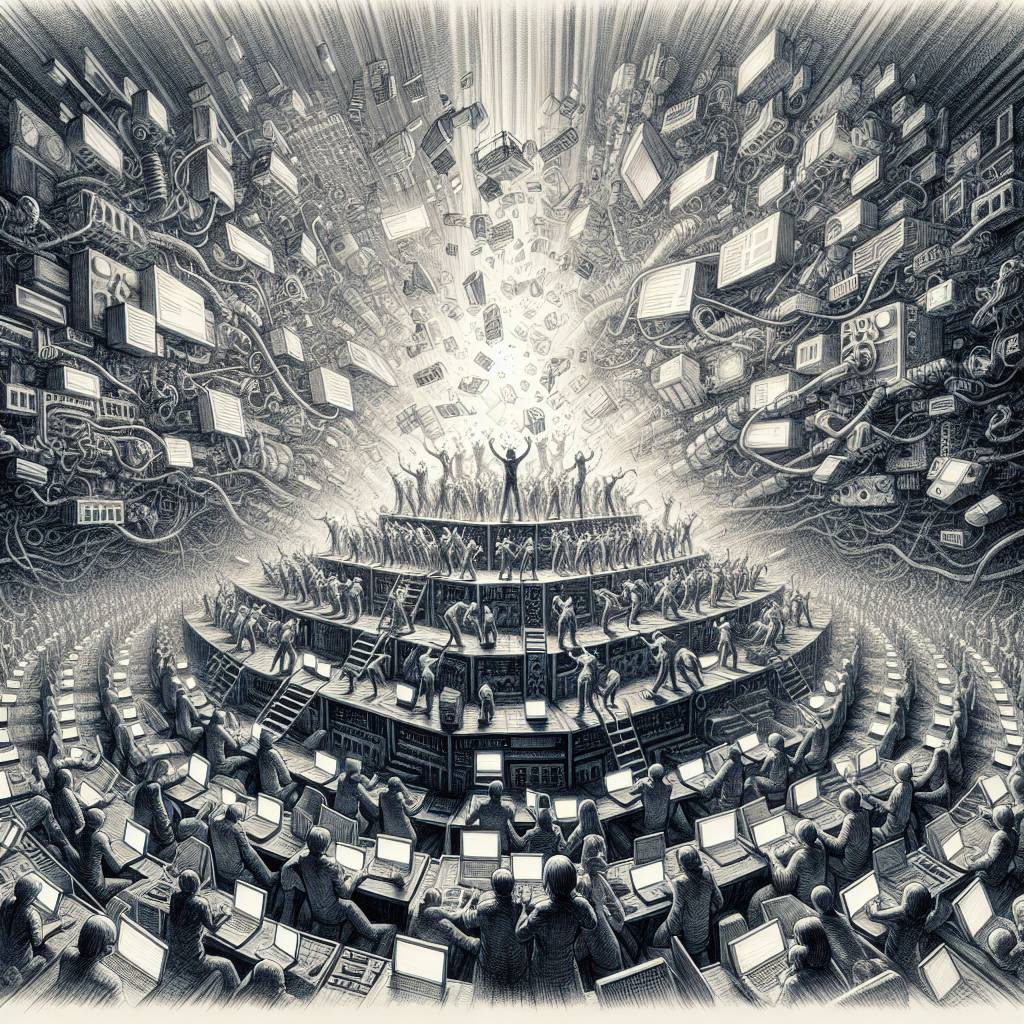
Well, it looks like Erlang’s Open Telecom Platform (OTP) just got a new career as an uninvited party crasher! With hackers exploiting the mother of all vulnerabilities, CVE-2025-32433 (rated a perfect 10 on the CVSS scale, because it’s just that special), this platform is practically rolling out the red carpet for cybercriminals. If your network was a bouncer, it just called in sick. Time to patch up, or you might just find your sensitive data headlining the next cybersecurity tabloid!
Key Points:
- CVE-2025-32433 is a critical RCE vulnerability in Erlang’s OTP Secure Shell daemon (sshd).
- This vulnerability allows attackers to execute commands without authentication.
- Vulnerable versions include Erlang/OTP before releases OTP-27.3.3, OTP-26.2.5.11, and OTP-25.3.2.20.
- Healthcare, agriculture, media, entertainment, and high-tech sectors are most affected.
- Mitigation includes patching and possibly disabling the SSH server or restricting access.
