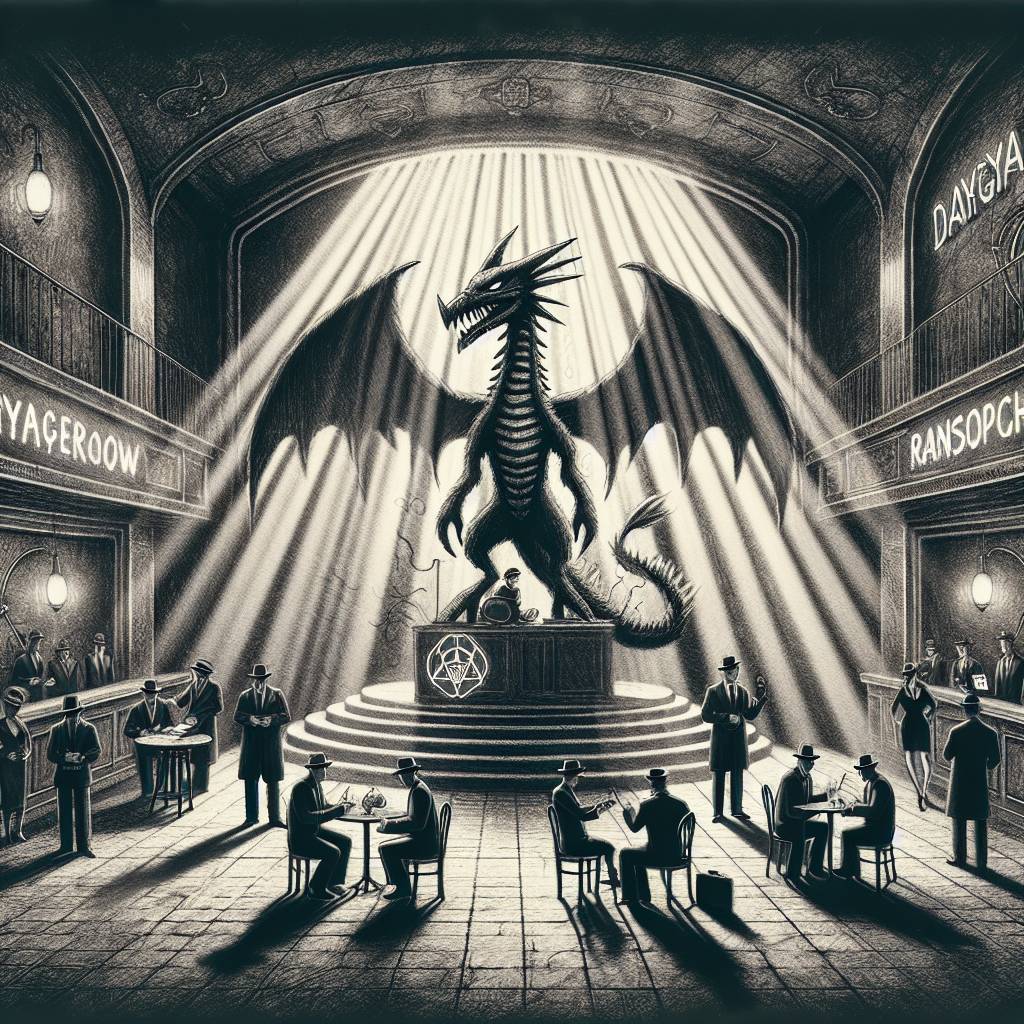
DragonForce Ransomware: The Cybercrime Cartel Comedy Club You Didn’t Want an Invite To
DragonForce is the new ransomware group on the block, with cartel-like ambitions and Conti’s leaked source code as its foundation. They’ve shifted from a ransomware-as-a-service model to a self-styled cartel, encouraging affiliates to create branded variants. DragonForce might not be breathing fire, but it’s certainly spreading it across networks.
Hot Take:
Just when you thought the world of cybercrime couldn’t get any more like an episode of a crime drama, DragonForce enters the scene with a plot twist worthy of a telenovela. With its ambitious cartel-like structure, this new ransomware group is channeling its inner mob boss, complete with encryption as its weapon of choice. Grab your popcorn, folks; this is the cybercrime saga you never knew you needed.
Key Points:
- DragonForce utilizes Conti’s leaked source code for its ransomware operations.
- The group has evolved from a ransomware-as-a-service model to a cartel-like structure.
- They employ ChaCha20 and RSA encryption, a nod to their Conti roots.
- DragonForce is recruiting affiliates to create their own branded ransomware variants.
- Security experts recommend robust defenses, including backups and network segmentation.
