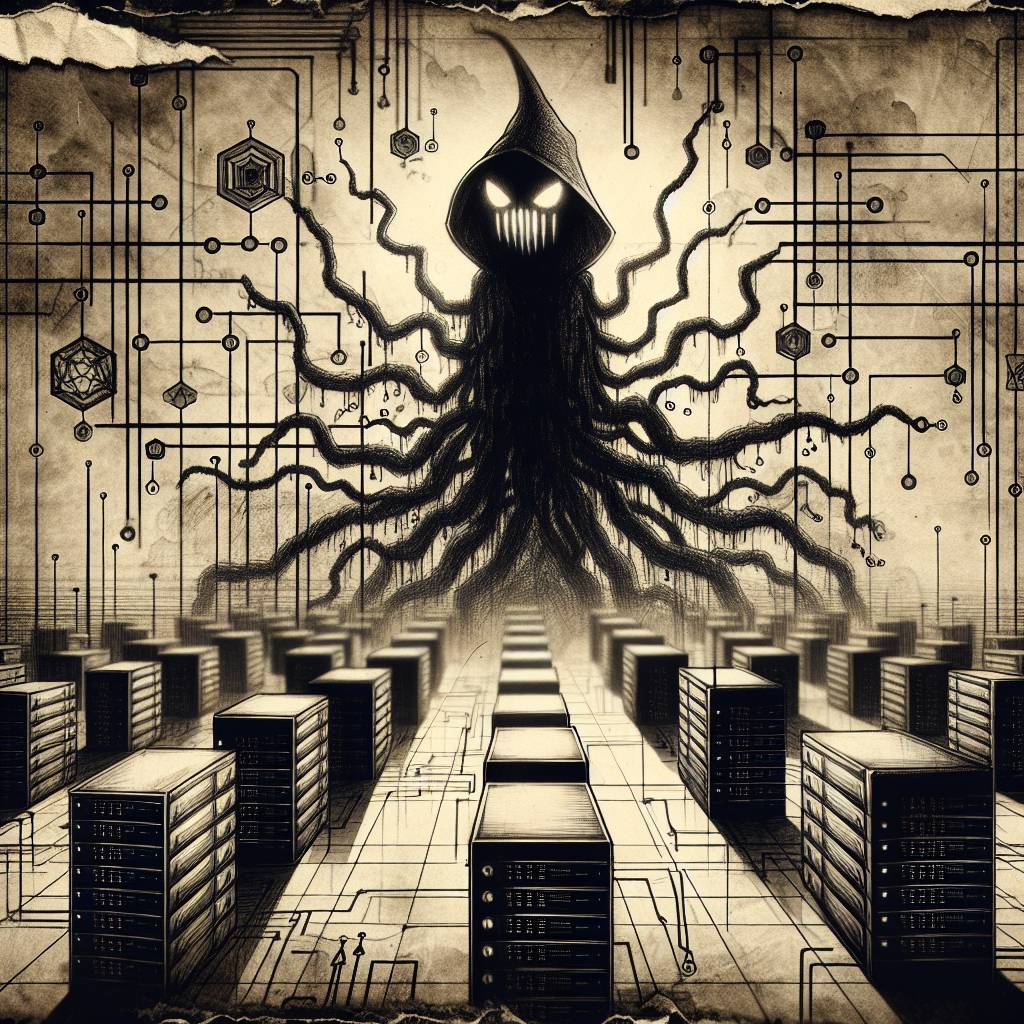
Docker Danger: Evolving Botnet Threat Unleashes Complex Malware Attack
A threat actor’s malicious tooling is evolving from simple cryptomining to potentially laying the groundwork for a complex botnet. By targeting exposed Docker APIs, it’s like upgrading from a slingshot to a high-tech catapult, with Akamai researchers noting this could be the start of a multi-vector threat extravaganza.
Hot Take:
Docker’s got docked! Docker APIs are the latest victim in the cybercriminal’s playbook, and it seems like they’ve been given a major upgrade with a splash of botnet-building flair. Looks like the only thing not getting a makeover here is the docker daemon’s wardrobe!
Key Points:
- Cyber baddies are targeting exposed Docker APIs to build a complex botnet.
- The new malicious payload blocks access to the compromised Docker API ports.
- Infection uses a modified Alpine Linux image and Tor network for anonymity.
- Tooling allows self-replication by infecting other Docker APIs autonomously.
- Potential future threats include credential theft and DDoS attacks.
Already a member? Log in here
