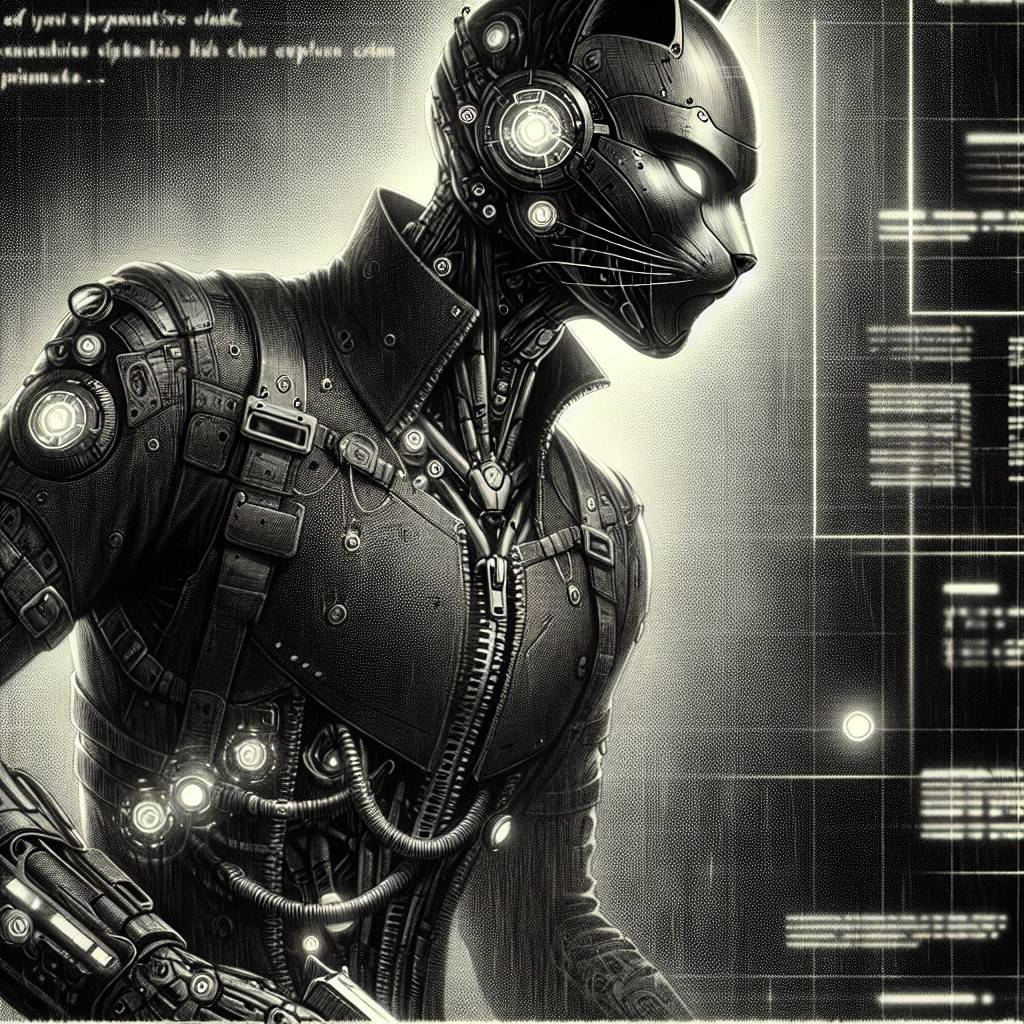
Cyber Cat Burglar Strikes: WSUS Flaw Brews ShadowPad Attack!
Attackers have found a new way to play “shadow” games with ShadowPad, exploiting the freshly patched WSUS RCE flaw CVE-2025-59287. Using PowerCat, they opened a shell, deploying ShadowPad malware faster than you can say “unauthorized access.” Organizations, patch up and lock those digital doors!
Hot Take:
Oh, WSUS, what a tangled web you weave – attackers were barely waiting for the ink to dry on the patch notes before they decided to crash the party with ShadowPad! If WSUS was a nightclub, it would definitely be the one with the bouncer who keeps letting the wrong people in. Time to tighten up those ropes, folks!
Key Points:
– A patched vulnerability (CVE-2025-59287) in WSUS was exploited to deliver ShadowPad malware.
– Attackers used PowerCat to obtain a shell and certutil and curl to install the malware.
– ShadowPad is a sophisticated backdoor linked to China-based APT groups.
– The WSUS flaw allowed remote code execution with system privileges.
– ASEC researchers recommend patching and restricting WSUS server access.
