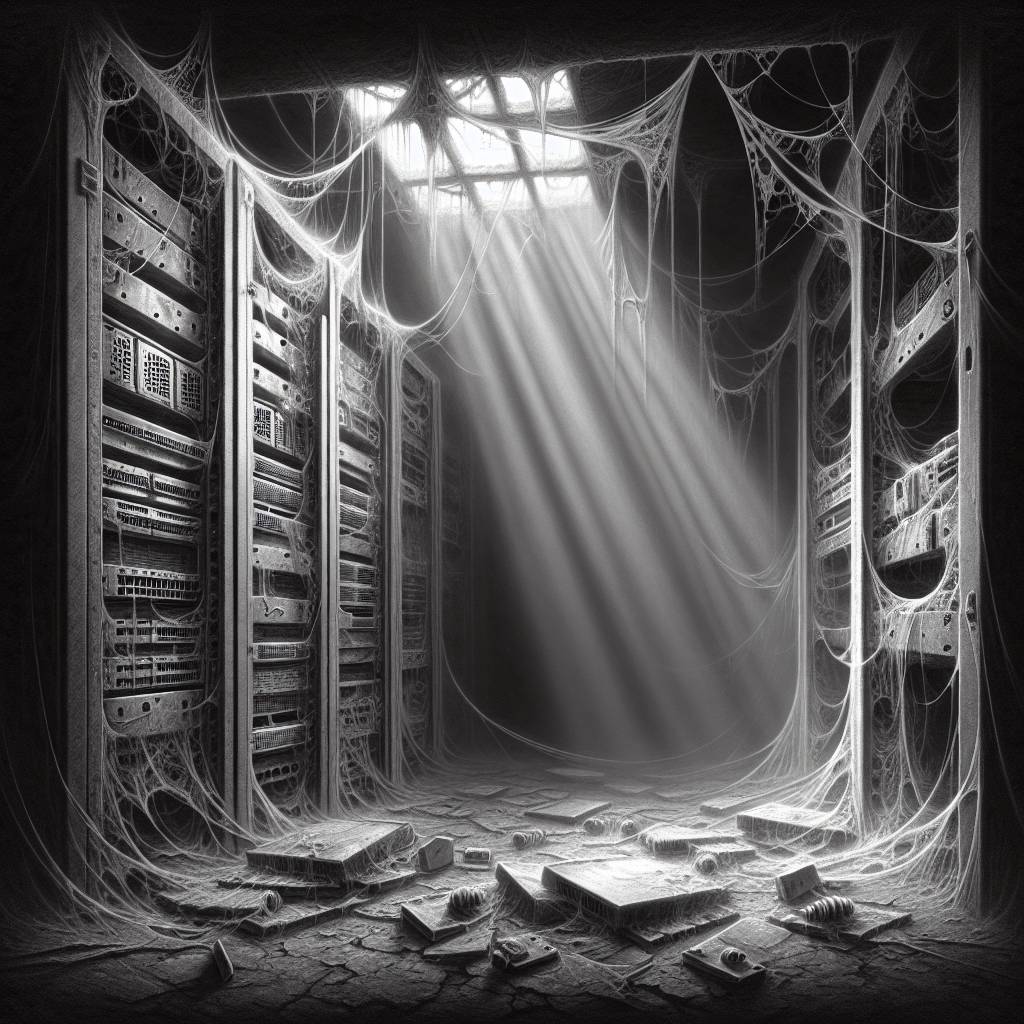
Cisco’s HTTP Server Fiasco: Is Your Network Vulnerable?
If your Cisco device is running a vulnerable Cisco IOS XE Software with the HTTP Server feature enabled, it could be like leaving your front door wide open. To check if your device is inviting trouble, run the show running-config | include ip http server|secure|active command and see if you need a locksmith!
Hot Take:
Oh, Cisco, not this again! It seems like just yesterday we were chatting about the latest patch and here we are, déjà vu with another vulnerability. It’s like a never-ending game of cybersecurity whack-a-mole, but instead of moles, it’s the HTTP Server feature causing a ruckus. Someone call tech support, stat!
Key Points:
- Cisco devices running vulnerable IOS XE Software with the HTTP Server feature enabled are at risk.
- Use the CLI command to check if the HTTP Server feature is enabled on your device.
- The presence of the “ip http server” or “ip http secure-server” command indicates vulnerability.
- Additional configurations can render the vulnerability non-exploitable over HTTP/HTTPS.
- See the Fixed Software section for information on vulnerable software releases.
Already a member? Log in here
