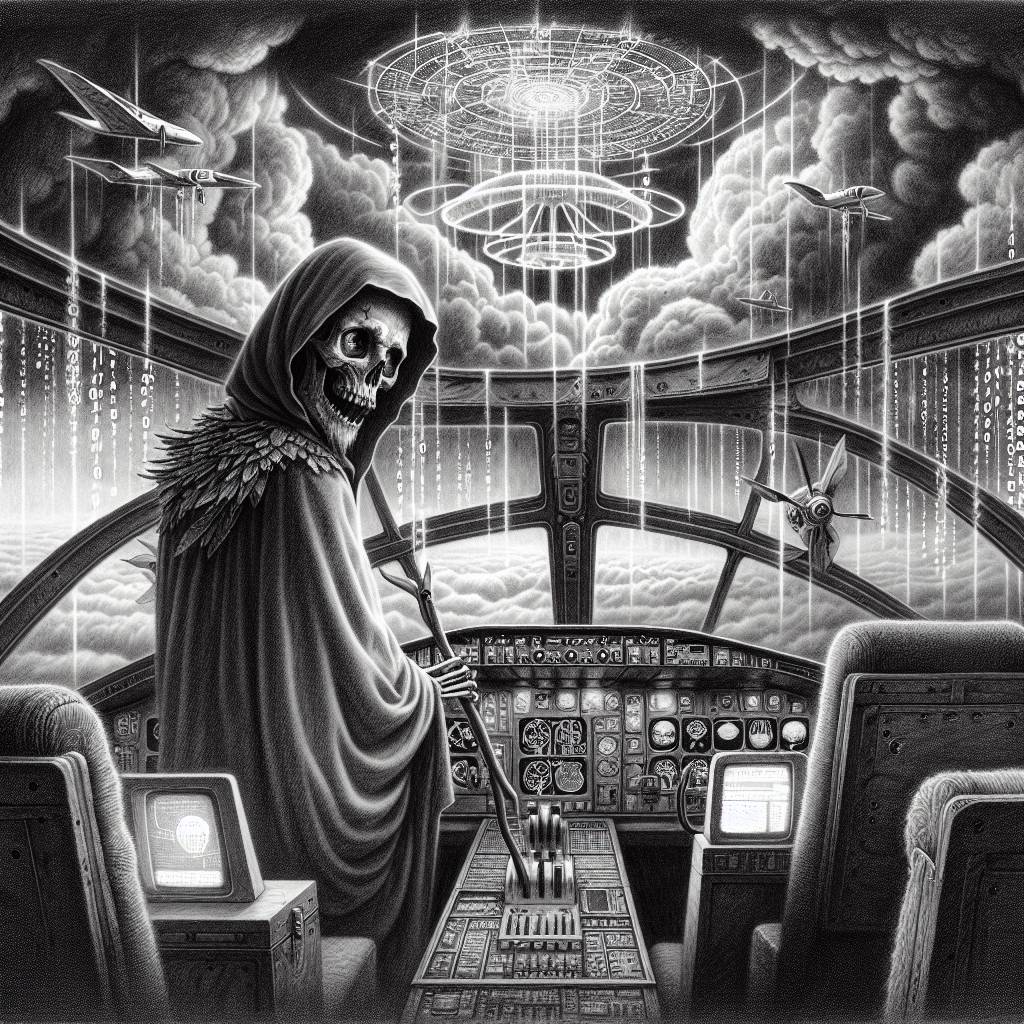
Charon Takes Flight: New Ransomware Targets Middle East Aviation in Cyber Comedy of Errors
Charon ransomware is targeting the Middle East’s public sector and aviation industry with tactics reminiscent of advanced persistent threat groups. This new kid on the block is causing quite a stir, employing sophisticated evasion techniques that make it a tough nut to crack for cybersecurity experts. Keep your digital doors locked!
Hot Take:
Looks like the Middle East’s public sector and aviation industry have been cordially invited to Charon’s latest ransomware rave. Instead of a DJ, this party’s got DLL side-loading, and they’re playing all the APT hits. Just remember, what happens in the server room, stays in the server room—until it doesn’t!
Key Points:
- Charon’s ransomware campaign is targeting the Middle East’s public sector and aviation industry.
- Threat actors are using advanced techniques resembling APT groups, including DLL side-loading.
- Charon’s ransomware employs multithreading for faster encryption and a BYOVD attack method that’s still under development.
- The campaign is likely targeted, using custom ransom notes specific to victims.
- There’s debate over whether Earth Baxia is directly involved or being impersonated.
Already a member? Log in here
