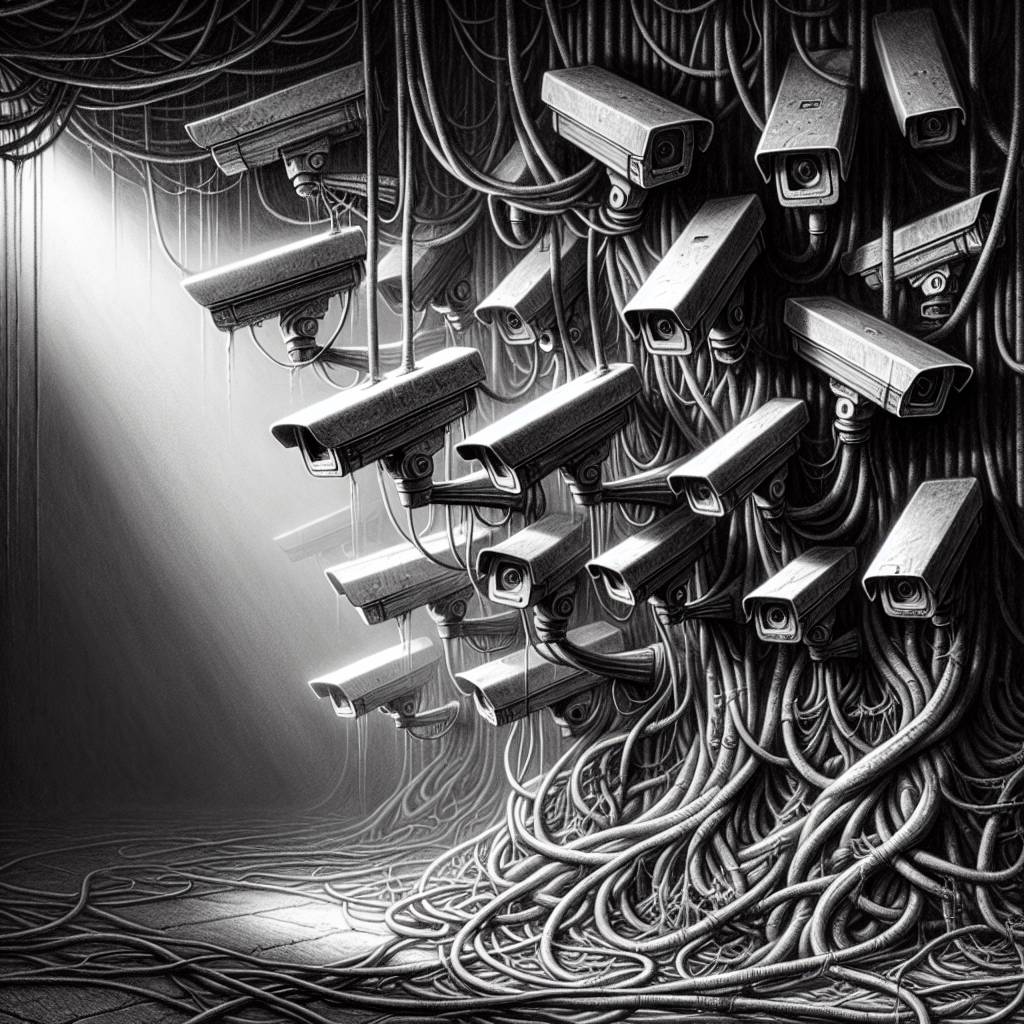
Botnet Bonanza: Unpatched Edimax IP Cameras Turn into Cyber Snares!
Botnets are exploiting a critical Edimax IP camera vulnerability, CVE-2025-1316, disclosed by CISA. Attackers are leveraging default credentials to access and execute remote commands. Despite this, Edimax isn’t patching the legacy cameras, leaving users to deal with the fallout. It’s a classic case of ‘out of sight, out of support.’
Hot Take:
Ah, the sweet irony of an IP camera designed to watch over us now being the one needing a watchdog! Looks like Edimax has decided to play hide and seek with security patches, and unfortunately, we’re all “it.” Who knew your IP camera could moonlight as a botnet contributor? Time to make your security system less of an open house for hackers and more of a Fort Knox.
Key Points:
– Edimax IP cameras are vulnerable to a critical command injection flaw, CVE-2025-1316.
– The vulnerability, disclosed by CISA, allows remote command execution through crafted requests.
– Multiple Mirai-based botnets are exploiting this vulnerability.
– Edimax has not patched the flaw, citing the devices as “legacy products.”
– Akamai has observed the flaw being actively exploited since fall 2024.
