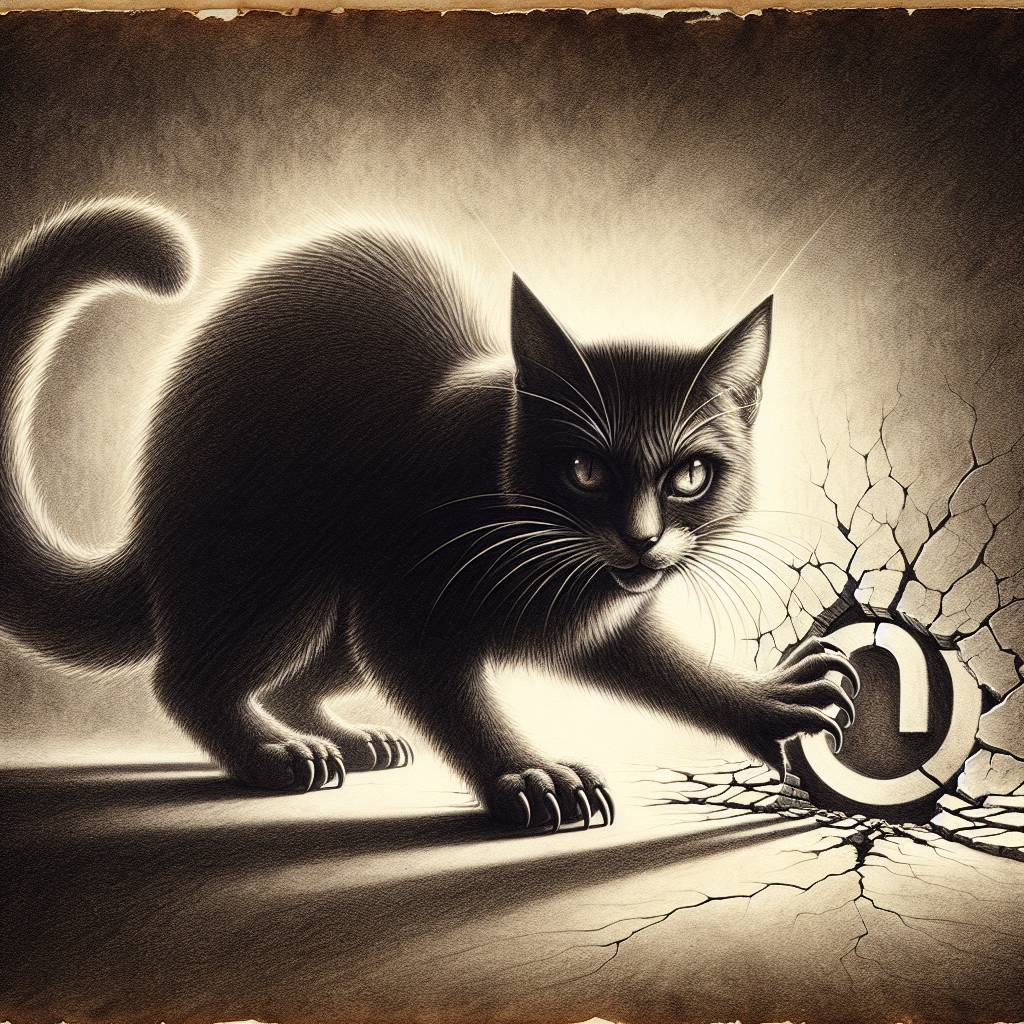
Bootkitty Pounces on LogoFAIL: A Cat-astrophic Threat for Unpatched Linux Devices
Bootkitty, a newly discovered Linux UEFI bootkit, exploits the LogoFAIL flaw to target vulnerable firmware, specifically in some Lenovo devices. While it’s not yet a widespread threat, it serves as a humorous reminder to update your firmware—because who knew that malicious BMP files could be the latest trend in computer fashion?
Hot Take:
Another day, another cyber villain with a feline flair. Meet Bootkitty, the latest software baddie to claw its way into our lives, exploiting the LogoFAIL flaw to turn your computer into its personal scratching post. But don’t worry, it’s still in its nine lives of development and mainly targeting specific Ubuntu versions. So if you’re not running Linux, you might escape with just a few cat hairs on your lap.
Key Points:
- Bootkitty is the first UEFI bootkit specifically targeting Linux.
- Exploits the LogoFAIL flaw, CVE-2023-40238, in UEFI firmware.
- Currently impacts specific Ubuntu versions and some Lenovo devices.
- Bootkitty uses shellcode embedded within BMP files to bypass security measures.
- Many devices remain vulnerable due to unpatched firmware against LogoFAIL.
Already a member? Log in here
