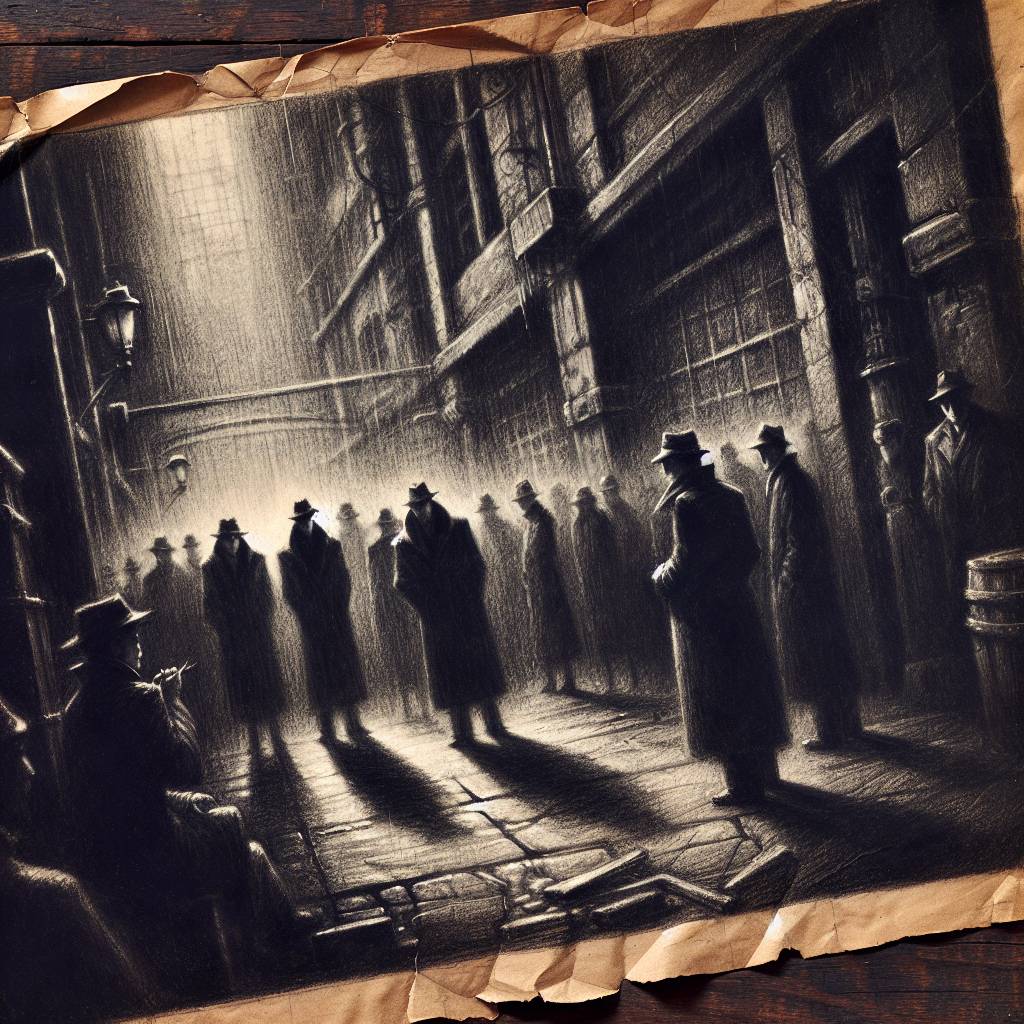
Bitter Truth: State-Backed Hackers Unleash Indian Intelligence with a Side of Malware Mayhem
Bitter is no sweet deal! This state-backed hacking group, aligned with Indian interests, has a diverse toolset for espionage. Known for targeting South Asian entities, Bitter now sets sights on new regions. Their favorite pastime? Spear-phishing with malware-laden emails, proving that when it comes to cyber mischief, Bitter is a spicy player!
Hot Take:
It’s a bird, it’s a plane, no, it’s Bitter, the hacking group with more aliases than a secret agent in a spy movie! With a penchant for cloak-and-dagger operations, Bitter’s espionage antics span continents and countries, leaving a trail of malware and confusion in their wake. Clearly, they’ve got the whole world as their stage, and they’re making the most of their starring role. Watch out, James Bond, Bitter’s coming for your title!
Key Points:
– Bitter, also known as APT-C-08, is a state-backed hacking group linked to the Indian government.
– Their targets include South Asian entities, with recent expansions into Turkey, China, and beyond.
– Bitter’s attack methods include spear-phishing emails and masquerading as government bodies.
– Key malware tools in their arsenal include ArtraDownloader, Keylogger, and Almond RAT.
– Operations often align with Indian Standard Time, hinting at their geographical base.
