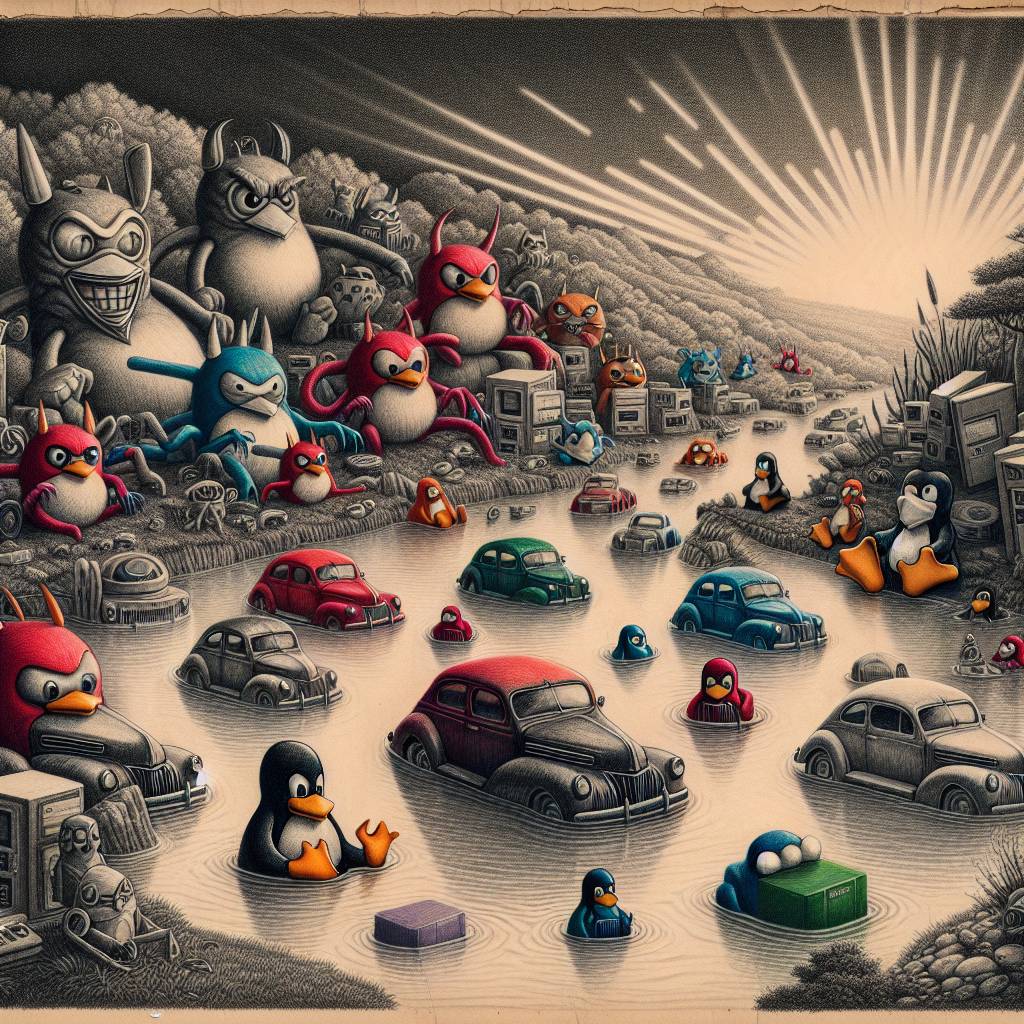
Auto-Color Chaos: SAP Vulnerability Exploits Linux Systems in Hilarious Malware Debut
A new malware campaign targets Linux systems by exploiting a SAP NetWeaver vulnerability. Auto-Color, a backdoor malware, was deployed against a US chemicals company. The campaign highlights the need for SAP security integration into broader IT operations, as attackers creatively leverage known vulnerabilities like CVE-2025-31324 in multi-stage attacks.
Hot Take:
Remember when Linux was the cool, invulnerable kid on the block that everyone admired for its security chops? Well, even the mighty fall, and this time it’s thanks to some sneaky cybercriminals who have discovered a secret SAP vulnerability dance. Apparently, the Auto-Color malware is teaching Linux a few new “moves,” and not the kind you’d want to show off at a party.
Key Points:
– A new malware, Auto-Color, is exploiting a critical vulnerability in SAP NetWeaver to target Linux systems.
– The attack was first observed in April 2025 when a US-based chemicals company was compromised.
– Auto-Color functions as a Remote Access Trojan (RAT) that adapts based on system privileges.
– The malware uses sophisticated evasion tactics, including disguising its presence and manipulating preload settings.
– Darktrace’s Autonomous Response blocked the malware’s outbound connections, preventing further damage.
