Amazon’s NPM Discovery: The Comedy of Errors in Supply Chain Security
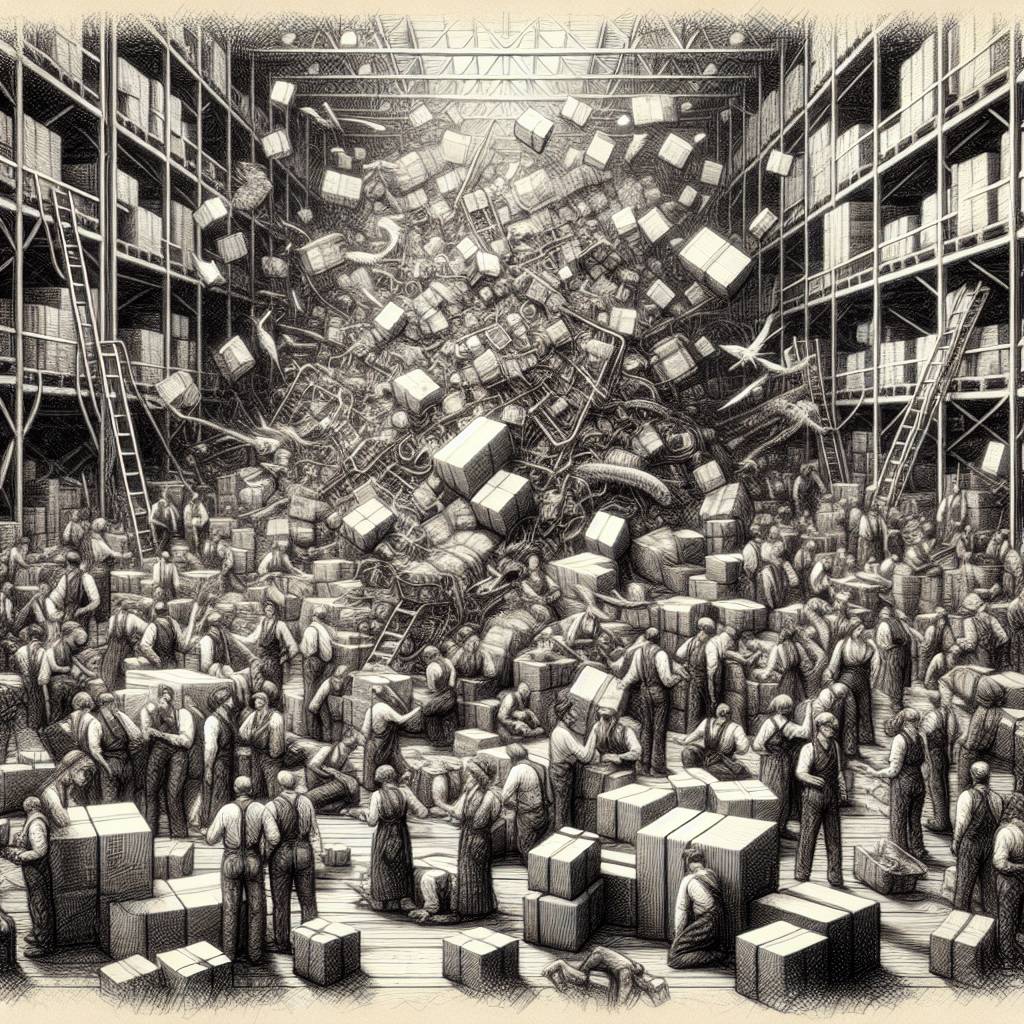
Amazon researchers uncovered a whopping 150,000 malicious packages in the NPM registry, marking a “defining moment in supply chain security.” These packages were part of a token farming campaign targeting the tea.xyz protocol, cleverly exploiting blockchain rewards without using overtly malicious code. It’s a new twist in the world of supply chain attacks.
Hot Take:
Looks like the NPM registry got a little too “tea”-rific with over 150,000 malicious packages, making this a sippin’ scandal and a supply chain security wake-up call! Forget the Earl Grey, developers are getting served a hot cup of trouble with a side of blockchain mischief.
Key Points:
- Amazon researchers unearthed over 150,000 malicious NPM packages in a token farming campaign.
- The campaign targeted the tea.xyz protocol, exploiting blockchain rewards without overtly malicious code.
- Threat actors used automated replication to artificially inflate package metrics for financial gain.
- Amazon and OpenSSF collaborated to assign identifiers to the nefarious packages.
- Recommendations include auditing NPM packages and strengthening software supply chain security.
Already a member? Log in here
