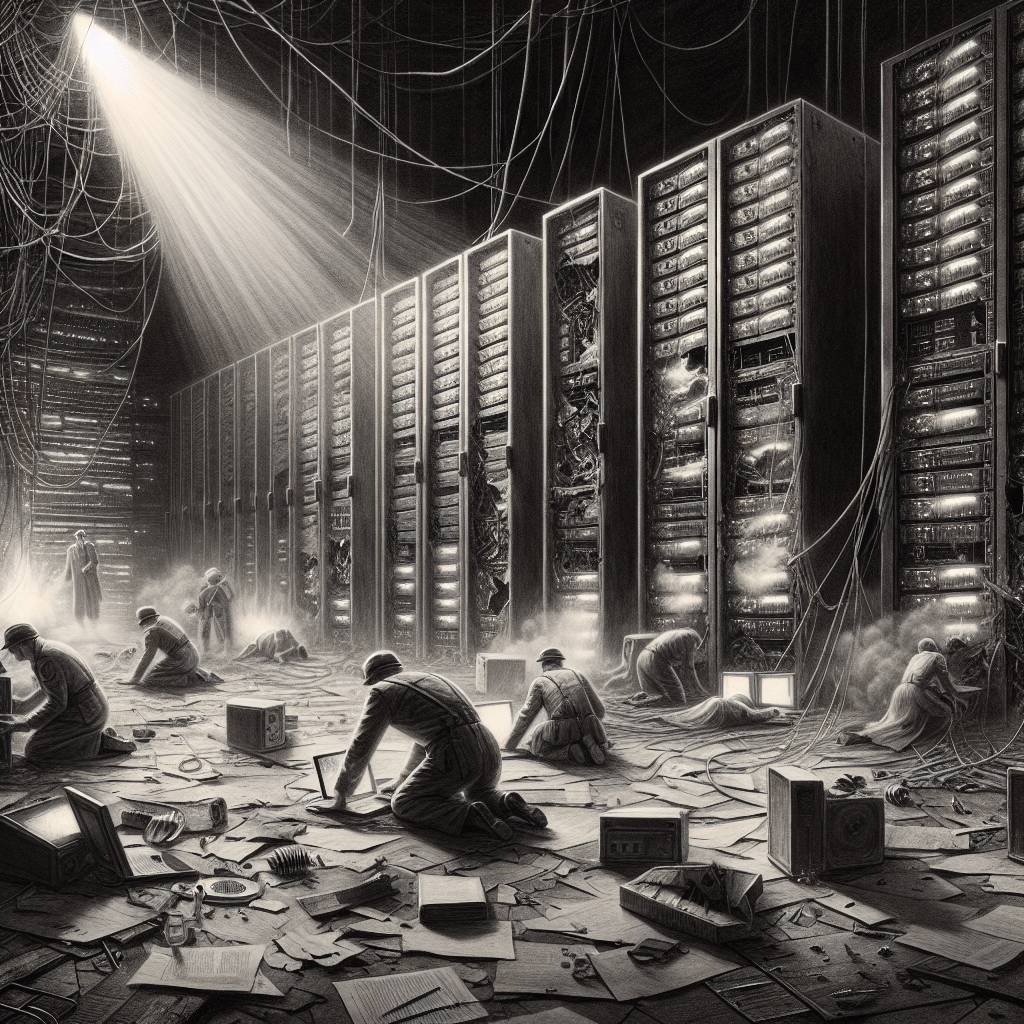
700+ Gogs Git Servers Hacked: The Zero-Day Comedy of Errors Continues!
Batten down the hatches, folks! Over 700 Gogs instances have been compromised through an unpatched zero-day vulnerability. This digital bug, CVE-2025-8110, lets attackers overwrite files outside the repository and execute remote code. So, if you’re running Gogs version 0.13.3 or older, it’s time to fix your Git sitch pronto!
Hot Take:
Looks like Gogs just got goggled! Someone let 700 instances slip through the cracks with a zero-day vulnerability that was as sneaky as a cat burglar in a top hat. Maybe it’s time for Gogs to put on its big boy shoes and patch up those holes before more servers get whisked away in the night!
Key Points:
- Over 700 Gogs instances compromised due to a zero-day vulnerability.
- Vulnerability tracked as CVE-2025-8110, related to improper symbolic link handling.
- Attackers can overwrite files and achieve remote code execution.
- Over 1,400 Gogs instances are exposed, with more than 700 already affected.
- A patch is in development, but not yet available as of December 10.
Already a member? Log in here
